Electronic Voting System is Vulnerable to Tampering
Avi Rubin, technical director of the Information Security Institute at Johns Hopkins University <br> <br>Photo by Will Kirk
Computer Researchers Find Critical Flaws in Popular Software Produced for U.S. Elections
The software believed to be at the heart of an electronic voting system being marketed for use in elections across the nation has weaknesses that could easily allow someone to cast multiple votes for one candidate, computer security researchers at The Johns Hopkins University have determined.
The researchers reached this conclusion after studying computer code believed to be for Ohio-based Diebold Election Systems’ electronic voting equipment. The code, which included modifications made through 2002, was posted anonymously to a public Web site earlier this year. During 2002, approximately 33,000 Diebold voting stations, which allow ballots to be cast via a 15-inch touch-screen monitor, were used in elections in Georgia, California, Kansas and other locations, according to a company news release. On July 21, the company finalized an agreement with the state of Maryland to provide up to $55.6 million in touch-screen voting technology and related services.
But after analyzing tens of thousands of lines of programming code purportedly used to make this electronic voting system work, three researchers from the Information Security Institute at Johns Hopkins, aided by a computer scientist at Rice University in Houston, have expressed serious concerns about the voting system. The researchers said they uncovered vulnerabilities in the system that could be exploited by an individual or group intent on tampering with election results. In particular, they pointed to the use of a “smart card,” containing a tiny computer chip, that each eligible voter receives. The card, inserted into the electronic voting machine, is designed to ensure that each person casts only one ballot. But the researchers believe a voter could hide a specially programmed counterfeit card in a pocket, withdraw it inside the booth and use it to cast multiple votes for a single candidate.
“A 15-year-old computer enthusiast could make these counterfeit cards in a garage and sell them,” said Avi Rubin, technical director of the Information Security Institute at Johns Hopkins and one of the researchers involved in the study. “Then, even an ordinary voter, without knowing anything about computer code, could cast more than one vote for a candidate at a polling place that uses this electronic voting system.”
The researchers were quick to note that no evidence exists that anyone has used such tactics to tamper with an election. However, they chose to make their findings public because of concerns that election fraud will almost certainly occur if weaknesses in the electronic voting system are not addressed before many more jurisdictions move to this method of picking public officials.
The security flaws were discovered this summer after Rubin assigned Adam Stubblefield, 22, and Yoshi Kohno, 25, two computer science doctoral students at the institute, to review the voting software code found on the Web. The students analyzed only those files that were publicly accessible and did not attempt to breach others that were protected by passwords. “Many of the attacks are very simple,” Kohno said. “It is unfortunate to find such flaws in a system potentially as important as this one.” Stubblefield added, “When people vote in the United States, they have to believe the election is fair.”
The researchers, joined by Dan Wallach, an assistant professor of computer science at Rice University, were able to reconstruct the electronic voting terminal in a Johns Hopkins computer lab and detected the security problems. “Even without access to the protected files, we’ve determined this system is fundamentally flawed,” Rubin said. “There will be no easy fix for this.”
The issue is important, Rubin said, because problems related to Florida’s punch card ballots during the 2000 Presidential election have prompted many cities and states to consider computer screen voting systems as a better alternative. But Rubin, who has conducted extensive research into electronic voting and has been tapped to review the security of a federal electronic voting proposal, said the move to high-tech balloting should not be conducted in haste. “People are rushing too quickly to computerize our method of voting before we know how to do it securely,” he said.
The researchers have detailed their findings in a technical paper
Although the researchers have not independently verified the current or past use of the code by Diebold or that the code they analyzed is actually Diebold code, they stated in their technical paper that “the copyright notices and code legacy information in the code itself are consistent with publicly available systems offered by Diebold and a company it acquired in 2001, Global Election Systems. Also, the code itself compiled and worked as an election system consistent with Diebold’s public descriptions of its system.”
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
A universal framework for spatial biology
SpatialData is a freely accessible tool to unify and integrate data from different omics technologies accounting for spatial information, which can provide holistic insights into health and disease. Biological processes…
How complex biological processes arise
A $20 million grant from the U.S. National Science Foundation (NSF) will support the establishment and operation of the National Synthesis Center for Emergence in the Molecular and Cellular Sciences (NCEMS) at…
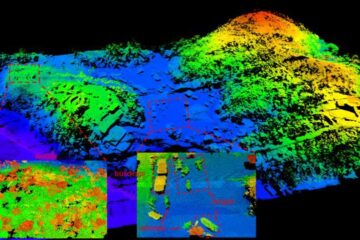
Airborne single-photon lidar system achieves high-resolution 3D imaging
Compact, low-power system opens doors for photon-efficient drone and satellite-based environmental monitoring and mapping. Researchers have developed a compact and lightweight single-photon airborne lidar system that can acquire high-resolution 3D…





















