Identity thieves’ "phishing" attacks could soon get a lot nastier
<br>"Phishing" e-mails appear to be sent by legitimate businesses, but are actually created and distributed by thieves who are trying to steal personal information. Photo by: David Bricker
The number of people who succumb to identity thieves’ “phishing” e-mails could go way up if immediate action isn’t taken to preempt the next generation of attacks, according to Markus Jakobsson, an Indiana University School of Informatics researcher.
A report by cybersecurity expert Jakobsson describing worst-case phishing scenarios was recently cited by Howard Schmidt, chief information security officer for eBay Inc., during his testimony before a U.S. Congressional subcommittee on government reform. The report has also been presented to members of the U.S. Government Accountability Office and the Cyber Security Industry Alliance, based in Washington, D.C.
“I came up with the worst kind of attacks I could think of and then worked on how to defend against them,” said Jakobsson, who is associate director of IU’s Center for Applied Cybersecurity Research. “Phishers haven’t invented these attacks yet, but the phishing attacks that are happening now are getting more and more sophisticated.”
Today’s phishing e-mails are already pretty tricky. Many spoof legitimate companies’ domain names by linking not to legitimate domain names, such as “ebay.com,” but to misleading domain names, like “secure-ebay.com,” which are owned by phishers. Some users, encountering fake Web sites that look real, unwittingly give away vital personal information such as social security numbers, bank account numbers, access codes, usernames and passwords. Another version of phishing takes advantage of the fact that many users configure their e-mail clients to display pictures and text formatting within the messages. This makes it possible for phishers to show users the name of a legitimate domain name within the body of their e-mails — while linking to a differently named Web site.
Phishing messages that appear to be sent by such trusted companies as eBay, Citibank and others are currently duping 3 percent of the people who receive them, according to a recent survey by Gartner Inc. Aware of the threat, members of Congress are currently debating passage of the Internet Spyware Prevention Act, which would provide the Justice Department with $10 million to apprehend phishers and other online scam artists.
Jakobsson said preliminary data suggest that savvier, “context-aware” phishing attacks could have success rates as high as 50 percent. Context-aware attacks, as Jakobsson envisions them, would take advantage of users’ unique circumstances or personal relationships.
One kind of context-aware attack Jakobsson describes tricks eBay bidders into giving out identifying information by leading bidders to believe they’ve won an auction. He also explains how eBay sellers can be victimized by context-aware attacks in which false payments lure sellers to give out their passwords.
In another kind of context-aware attack, a potential victim might receive a message from a known person — for example, a friend or loved one — asking him or her to go to a Web site to update banking information. But how would a phisher know who was related to whom and how? “There are personal and business networking Web sites out there, such as orkut.com, where users’ relationships are easily seen,” Jakobsson said. “A phisher can find out whether a person in your ’personal network’ list is a wife, a husband, a sister or a business associate, and take advantage of that.”
In a third kind of context-aware attack, the phisher first creates a believable (but fictitious) problem with a user’s online account and then asks for a user’s personal information to fix it. By analogy, current e-mail attacks are like phone repair personnel showing up out of the blue, claiming a potential victim’s phone lines aren’t working, when the victim can easily tell they are. “But now imagine I, the attacker, actually cut your telephone lines,” Jakobsson explained. “I wait for you to notice. Then I show up, claiming to be there to fix the problem. I appear legitimate and everything seems consistent, so you invite me onto your property. Whenever you get e-mails requesting personal information, no matter what the circumstances, be skeptical, even if what you’re seeing appears legitimate.”
Jakobsson admitted the scenarios may instill some paranoia, but he is joined by eBay’s Schimidt and others in his assessment that such context-aware attacks are inevitable. To combat the problem, Jakobsson believes users, online businesses and government must get involved. “A number of us are recommending changes in the way eBay and others display online information,” Jakobsson said. “Personal information should only be displayed publicly on Web sites if it is absolutely necessary, or if a user gives his or her specific assent, knowing the risks. Government can help by requesting or requiring these changes. And of course there must be a public awareness campaign.”
The report, “Modeling and Preventing Phishing Attacks,” is currently being considered for the International Financial Cryptography Association’s annual meeting in February 2005. Copies of the paper are available to journalists and scholars only upon request. The research was supported by RSA Laboratories in Bedford, Mass.
Jakobsson is part of a group at IU that develops technological counter-measures to phishing and other types of Internet fraud. Members of the group are currently working on authentication software that would protect users from unknowingly entering PINs, usernames and passwords at illegitimate Web sites.
Media Contact
More Information:
http://www.indiana.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
A universal framework for spatial biology
SpatialData is a freely accessible tool to unify and integrate data from different omics technologies accounting for spatial information, which can provide holistic insights into health and disease. Biological processes…
How complex biological processes arise
A $20 million grant from the U.S. National Science Foundation (NSF) will support the establishment and operation of the National Synthesis Center for Emergence in the Molecular and Cellular Sciences (NCEMS) at…
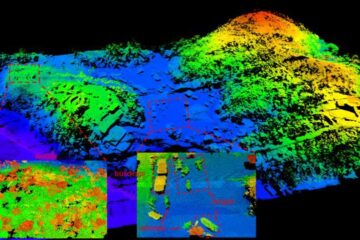
Airborne single-photon lidar system achieves high-resolution 3D imaging
Compact, low-power system opens doors for photon-efficient drone and satellite-based environmental monitoring and mapping. Researchers have developed a compact and lightweight single-photon airborne lidar system that can acquire high-resolution 3D…





















