The perfect clone: RUB researchers hack RFID smartcards

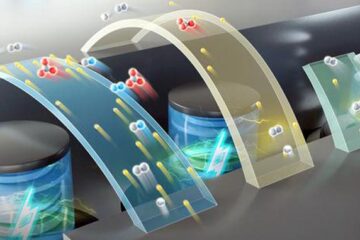
Measuring the electro-magnetic field<br>
Professional safecrackers use a stethoscope to find the correct combination by listening to the clicks of the lock. Researchers at the Ruhr-University Bochum have now demonstrated how to bypass the security mechanisms of a widely used contactless smartcard in a similar way. Employing so-called “Side-Channel Analysis” the researchers of the Chair for Embedded Security (Prof. Dr.-Ing. Christof Paar) can break the cryptography of millions of cards that are used all around the world.
Mathematically secure
RFID smartcards (Radio Frequency Identification) of the type DESFire MF3ICD40 are widely employed in payment and access control systems. The security of these cards is based on Triple-DES, a cipher that is unbreakable from a purely mathematic point of view. DESFire cards are for instance used by the public transport agencies in Melbourne, San Francisco and Prague. The DESFire MF3ICD40 is manufactured by NXP, the former semiconductor division of Philips Electronics.
Fluctuations of the magnetic field
A person is identified as a passenger, employee or customer when his RFID smartcard is placed in the proximity of a reader. To guarantee the necessary level of security, a secret key is stored on the integrated chip inside the card. But just like for the safe, the security mechanism produces the electronic equivalent of the clicks of a mechanic lock. “We measured the power consumption of the chip during the encryption and decryption with a small probe”, says David Oswald. The fluctuations of the electro-magnetic field allow the researchers to conclude to the full 112-bit secret key of the smartcard.
Low cost, big damage
Having extracted the keys, an attacker can create an unlimited number of undetectable clones of a given card. The required time and effort are quite low: “For our measurements, we needed a DESFire MF3ICD40 card, an RFID reader, the probe and an oscilloscope to measure the power consumption”, says Oswald. This equipment only costs a few thousand euros. Having obtained knowledge on the characteristic properties of the smartcard, the attack takes three to seven hours. The manufacturer NXP confirmed the security hole in the meanwhile and recommends his customers to upgrade to a newer version of the card.
Insufficient countermeasures
Already back in 2008, researchers around Prof. Dr.-Ing. Christof Paar used Side-Channel Analysis to break supposedly secure systems. Three years ago, garage and car doors “mysteriously” opened for the researchers of the Chair for Embedded Security. The employed KeeLoq RFID system – which customers and manufacturers trusted blindly before – turned out to be highly susceptible to Side-Channel Analysis.
Further information
Prof. Dr.-Ing. Christof Paar, Chair for Embedded Security, Building ID 2/607, Tel. +49 234 32 22994, christof.paar@rub.de
Homepage: http://www.emsec.rub.de
Media Contact
More Information:
http://www.emsec.rub.deAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
High-energy-density aqueous battery based on halogen multi-electron transfer
Traditional non-aqueous lithium-ion batteries have a high energy density, but their safety is compromised due to the flammable organic electrolytes they utilize. Aqueous batteries use water as the solvent for…

First-ever combined heart pump and pig kidney transplant
…gives new hope to patient with terminal illness. Surgeons at NYU Langone Health performed the first-ever combined mechanical heart pump and gene-edited pig kidney transplant surgery in a 54-year-old woman…
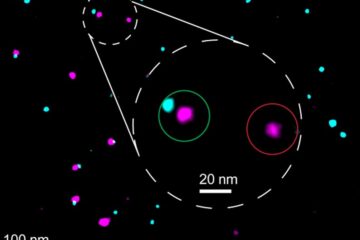
Biophysics: Testing how well biomarkers work
LMU researchers have developed a method to determine how reliably target proteins can be labeled using super-resolution fluorescence microscopy. Modern microscopy techniques make it possible to examine the inner workings…





















