IT security for the daily life: Withdrawing money at cash machines with 'Google Glass'

Mark Simkin wants to use "Google Glass" to withdraw money at a cash machine in such a secure way that no spying is possible. Credit: Oliver Dietze
But what IT experts celebrate as a new milestone makes privacy groups skeptical. So far, few people have access to the prototype to test how it can be used in daily life. “Thanks to the Max Planck Institute for Informatics we are one of the few universities in Germany that can do research with Google Glass”, says Dominique Schröder, assistant professor of Cryptographic Algorithms at Saarland University.
The futuristic-looking device consists of a glasses frame on which a camera and a mini computer are installed. It depicts information in the user's field of vision via a glass prism that is installed at the front end of the right temple. According to the German computer magazine “c't”, this causes an effect “as if the user were looking at a 24 inch screen from a distance of two and a half meters”. Schröder, who also does research at the Center for IT-Security, Privacy and Accountability (CISPA), located only a few yards away, is aware of the data security concerns with Google Glass:
“We know that you can use it to abuse data. But it can also be used to protect data.” To prove this, Schröder and his group combine “Google Glass” with cryptographic methods and techniques from automated image analysis to create the software system “Ubic”. By using Ubic, withdrawing money at a cash machine would change as follows: The customer identifies himself to the cash machine.
This requests from a reliable instance the public key of the customer. It uses the key to encrypt the one-way personal identification number (PIN) and seals it additionally with a “digital signature”, the digital counterpart of the conventional signature. The result shows up on the screen as a black-and-white pattern, a so-called QR code. The PIN that is hidden below is only visible for the identified wearer of the glasses. Google Glass decrypts it and shows it in the wearer's field of vision.”
Although the process occurs in public, nobody is able to spy on the PIN”, explains Schröder. This is not the case if PINs are sent to a smart phone. To spy on the PIN while it is being entered would also be useless, since the PIN is re-generated each time the customer uses the cash machine. An attacker also wearing a Google Glass is not able to spy on the process, either. The digital signature guarantees that no assailant is able to intrude between the customer and the cash machine as during the so-called “skimming”, where the assailant can impersonate the customer.
Only the customer is able to decrypt the encryption by the public key with his secret key. As long as this is safely stored on the Google Glass, his money is also safe. At the computer expo Cebit, the researchers will also present how Google Glass can be used to hide information. Several persons all wearing Google Glass can read the same document with encrypted text at the same time, but in their fields of vision they can only see the text passages that are intended for them.
“This could be interesting, for example, for large companies or agencies that are collecting information in one document, but do not want to show all parts to everybody”, explains Mark Simkin, who was one of the developers of Ubic. A large electric company has already sent a request to the computer scientists in Saarbrücken. Google Glass is expected to enter the American market this year.
Background information about computer science research at Saarland University in Germany
The Department of Computer Science represents the center of computer science research in Saarbrücken. Seven other worldwide renowned research institutes are close by the department: The Max Planck Institutes for Informatics and for Software Systems, the German Research Center for Artificial Intelligence (DFKI), the Center for Bioinformatics, the Intel Visual Computing Institute, the Center for IT Security, Privacy and Accountability (CISPA) and the Cluster of Excellence “Multimodal Computing and Interaction”.
More Information:
Project video: http://goo.gl/4mS0Jq
Further Questions:
Dominique Schroeder
Assistant Professor
Cryptographic Algorithms
Phone: +49 681 302-71922
Email: ds@ca.cs.uni-saarland.de
Mark Simkin
Cryptographic Algorithms
Email: simkin@ca.cs.uni-saarland.de
Editor:
Gordon Bolduan
Science Communication
Competence Center of Informatics
Phone: +49 (0)681 302-70741
Email: bolduan@mmci.uni-saarland.de
Media Contact
More Information:
http://www.uni-saarland.deAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
High-energy-density aqueous battery based on halogen multi-electron transfer
Traditional non-aqueous lithium-ion batteries have a high energy density, but their safety is compromised due to the flammable organic electrolytes they utilize. Aqueous batteries use water as the solvent for…

First-ever combined heart pump and pig kidney transplant
…gives new hope to patient with terminal illness. Surgeons at NYU Langone Health performed the first-ever combined mechanical heart pump and gene-edited pig kidney transplant surgery in a 54-year-old woman…
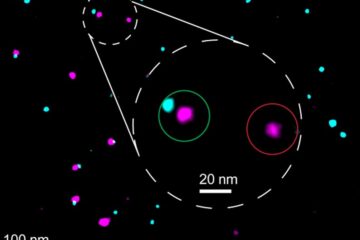
Biophysics: Testing how well biomarkers work
LMU researchers have developed a method to determine how reliably target proteins can be labeled using super-resolution fluorescence microscopy. Modern microscopy techniques make it possible to examine the inner workings…





















