IPv6 Guide Provides Path to Secure Deployment of Next-Generation Internet Protocol

Guidelines for the Secure Deployment of IPv6 (NIST Special Publication 800-119), describes the features of IPv6 and the possible related security impacts, provides a comprehensive survey of mechanisms to deploy IPv6 and suggests a deployment strategy for a secure IPv6 environment.
The ballooning popularity of devices, such as smart phones and netbooks, tied to the Internet is rapidly depleting the number of so-called IP addresses available under the current Internet Protocol version 4 (IPv4), so the networkers of the world are preparing to move to the next generation, IPv6. Among other improvements, IPv6 has a vastly greater number of potential addresses—several billion per each of the world’s current population of about 6.9 billion people.
To ensure that the federal government is prepared for IPv6, the Office of Management and Budget has mandated federal agencies to begin deploying the new protocol. NIST developed the IPv6 security guidelines in support of the Federal Information Security Management Act (FISMA). The publication is designed to help federal agencies avoid possible security risks that could occur during IPv6 deployment. It also could be useful for the private sector and other organizations.
“The Internet protocol pervades every aspect of computer communications,” explains lead author Sheila Frankel, “so deploying IPv6 is a major task.” With detailed planning, she says, organizations can navigate the process smoothly and securely. Most organizations will be operating IPv6 and IPv4 concurrently.
“Security will be a challenge, however, because organizations will be running two protocols and that increases complexity, which in turn increases security challenges,” Frankel says. SP 800-119 describes the security challenges organizations may face as they deploy IPv6. Those challenges include fending off attackers that have more experience than an organization in the early stages of IPv6 deployment and the difficulty of detecting unknown or unauthorized IPv6 assets on existing IPv4 production networks. The publication provides information to be considered during the deployment planning process and makes recommendations to mitigate IPv6 threats.
SP 800-119, Guidelines for the Secure Deployment of IPv6, may be downloaded in pdf format from http://csrc.nist.gov/publications/nistpubs/800-119/sp800-119.pdf. An index to the NIST 800-series special publications on computer security is available at http://csrc.nist.gov/publications/PubsSPs.html.
Media Contact
More Information:
http://www.nist.govAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
High-energy-density aqueous battery based on halogen multi-electron transfer
Traditional non-aqueous lithium-ion batteries have a high energy density, but their safety is compromised due to the flammable organic electrolytes they utilize. Aqueous batteries use water as the solvent for…

First-ever combined heart pump and pig kidney transplant
…gives new hope to patient with terminal illness. Surgeons at NYU Langone Health performed the first-ever combined mechanical heart pump and gene-edited pig kidney transplant surgery in a 54-year-old woman…
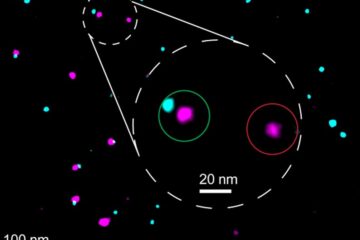
Biophysics: Testing how well biomarkers work
LMU researchers have developed a method to determine how reliably target proteins can be labeled using super-resolution fluorescence microscopy. Modern microscopy techniques make it possible to examine the inner workings…





















