System halts computer viruses, worms, before end-user stage

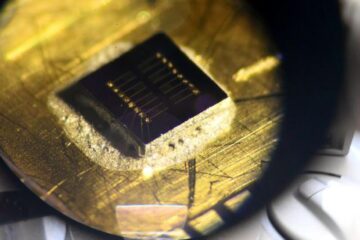
John Lockwood, Ph.D., assistant professor of computer science and engineering, programs the data enabling device to thwart the SoBig worm. Lockwood and his graduate students have approached the problem of halting worms and viruses via hardware instead of software. When a virus or worm is detected, the system either can drop the malicious traffic or generate a pop-up message on an end-user’s computer.
Scanning all of Shakespeare in 1/60th of a second
A computer scientist at Washington University in St. Louis has developed technology to stop malicious software – malware – such as viruses and worms long before it even has a chance to reach computers in the home and office.
John Lockwood, Ph.D., an assistant professor of computer science at Washington University, and the graduate students that work in his research laboratory have developed a hardware platform called the Field-programmable Port Extender (FPX) that scans for malware transmitted over a network and filters out unwanted data.
“The FPX uses several patented technologies in order to scan for the signatures of malware quickly,” said Lockwood. “Unlike existing network intrusion systems, the FPX uses hardware, not software, to scan data quickly. The FPX can scan each and every byte of every data packet transmitted through a network at a rate of 2.4 billion bits per second. In other words, the FPX could scan every word in the entire works of Shakespeare in about 1/60th of a second.”
Lockwood published his results in Military and Aerospace Programmable Logic Device (MALPD), Sept.,2003.
The paper is dowloadable online at:
http://www.arl.wustl.edu/~lockwood/publications/MAPLD_2003_e10_lockwood_p.pdf.
Computer virus and Internet worm attacks are aggravating, costly, and a threat to our homeland security. Recent attacks by Nimba, Code Red, Slammer, SoBigF, and MSBlast have infected computers globally, clogged large computer networks, and degraded corporate productivity. It can take weeks to months for Information Technology staff to clean up all of the computers throughout a network after an outbreak. The direct cost to recover from just the ’Code Red version two’ worm alone was $2.6 billion.
The United States has come to depend on computers to support its critical infrastructure. The nation’s power system, financial networks, and military infrastructure all rely on computers to operate. As a form of terrorism, a foreign agent could introduce a malignant worm or virus disguised as benign data to attack computers throughout a network. Terrorists could use this malware to bring down crucial components of our corporate infrastructure and military.
In much the same way that a human virus spreads between people that come in contact, computer viruses and Internet worms spread when computers come in contact over the Internet. Viruses spread when a computer user downloads unsafe software, opens a malicious attachment, or exchanges infected computer programs over a network. An Internet Worm spreads over the network automatically when malicious software exploits one or more vulnerabilities in an operating system, a Web server, a database application, or an email exchange system.
Existing firewalls do little to protect against such attacks. Once a few systems are compromised, they proceed to infect other machines, which in turn quickly spread throughout a network.
“As is the case with the spread of a contagious disease like SARS, the number of infected computers will grow exponentially unless contained,” Lockwood said. “The speed of today’s computers and vast reach of the Internet, however, make a computer virus or Internet worm spread much faster than human diseases. In the case of SoBigF, over one million computers were infected within the first 24 hours and over 200 million computers were infected within a week.”
Today, most Internet worms and viruses are not detected until after they reach an end-user’s personal computer. It is difficult for companies, universities, and government agencies to maintain network-wide security.
Unfair burden on end-users
“Placing the burden of detection on the end -user isn’t efficient or trustworthy because individuals tend to ignore warnings about installing new protection software and the latest security updates, “Lockwood pointed out. “New vulnerabilities are discovered daily, but not all users take the time to download new patches the moment they are posted. It can take weeks for an IT department to eradicate old versions of vulnerable software running on end-system computers.”
The high speed of the FPX is possible because the logic on the FPX is implemented as Field Programmable Gate Array (FPGA) circuits, Lockwood explained. These circuits are used to scan and filter Internet traffic for worms and viruses using FPGA circuits that operate in parallel. Lockwood’s group has developed and implemented circuits that process the Internet protocol (IP) packets directly in hardware. They also have developed several circuits that rapidly scan streams of data for strings or regular expressions in order to find the signatures of malware carried within the payload of Internet packets.
“On the FPX, the reconfigurable hardware can be dynamically reconfigured over the network to search for new attack patterns,” Lockwood said. “Should a new Internet worm or virus be detected, multiple FPX devices can be immediately programmed to search for their signatures. Each FPX device then filters traffic passing over the network, so that it can immediately quarantine a virus or Internet worms within sub networks (subnets). By just installing a few such devices between subnets, a single device can protect thousands of users. By installing multiple devices at key locations throughout a network, large networks can be protected.”
A local St. Louis company, Global Velocity, is building commercial systems that use the FPX technology. The company is working with local companies, international corporations, universities, and the government to make plans to install systems in both local-area and wide-area networks. The device self-integrates easily into existing Gigabit Ethernet or Asynchronous Transfer Mode (ATM) networks.
The FPX itself fits within a rack-mounted chassis that can be installed in any network closet. When a virus or worm is detected, the system can either silently drop the malicious traffic or generate a pop-up message on an end-user’s computer. An administrator uses a simple, web-based interface to control and configure the system.
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Sea slugs inspire highly stretchable biomedical sensor
USC Viterbi School of Engineering researcher Hangbo Zhao presents findings on highly stretchable and customizable microneedles for application in fields including neuroscience, tissue engineering, and wearable bioelectronics. The revolution in…

Twisting and binding matter waves with photons in a cavity
Precisely measuring the energy states of individual atoms has been a historical challenge for physicists due to atomic recoil. When an atom interacts with a photon, the atom “recoils” in…
Nanotubes, nanoparticles, and antibodies detect tiny amounts of fentanyl
New sensor is six orders of magnitude more sensitive than the next best thing. A research team at Pitt led by Alexander Star, a chemistry professor in the Kenneth P. Dietrich…





















