New computer security guide can help safeguard your small business

The guide, Small Business Information Security: The Fundamentals, was authored by Richard Kissel, who spends much of his time on the road teaching computer security to groups of small business owners ranging from tow truck operators to managers of hospitals, small manufacturers and nonprofit organizations.
The 20-page guide uses simple and clear language to walk small business owners through the important steps necessary to secure their computer systems and data.
Small businesses make up more than 95 percent of the nation's businesses, are responsible for about 50 percent of the Gross National Product and create about 50 percent of the country's new jobs, according to a 2009 Small Business Administration report. Yet these organizations rarely have the information technology resources to protect their sensitive information that larger corporations do.
Consequently, they could be seen as easy marks by hackers and cyber criminals, who could easily focus more of their unwanted attention on small businesses. And just like big companies, the computers at small businesses hold sensitive information on customers, employees and business partners that needs to be guarded, Kissel says. He adds that regulatory agencies have requirements to protect some health, financial and other information.
“There's a very small set of actions that a small business can do to avoid being an easy target, but they have to be done and done consistently,” Kissel says.
In the guide Kissel provides 10 “absolutely necessary steps” to secure information, which includes such basics as installing firewalls, patching operating systems and applications and backing up business data, as well as controlling physical access to network components and training employees in basic security principles.
He also provides 10 potential security trouble spots to be aware of such as e-mail, social media, online banking, Web surfing and downloading software from the Internet, as well as security planning considerations. The guide's appendices provide assistance on identifying and prioritizing an organization's information types, recognizing the protection an organization needs for its priority information types and estimating the potential costs of bad things happening to important business information.
NIST works with the Small Business Administration and the Federal Bureau of Investigation in this outreach to educate small businesses.
Small Business Information Security: The Fundamentals can be downloaded from the Small Business Corner Web site at http://www.csrc.nist.gov/groups/SMA/sbc/.
The related video, “Information Technology Security for Small Business. It's not just good business. It's essential business,” features experts from NIST and the Small Business Administration. The video is available on You Tube and the Small Business Corner of the NIST Computer Security Web pages. A free DVD of the video may be obtained by contacting Rich Kissel at (301) 975-5017 or by email at richard.kissel@nist.gov
Media Contact
More Information:
http://www.nist.govAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
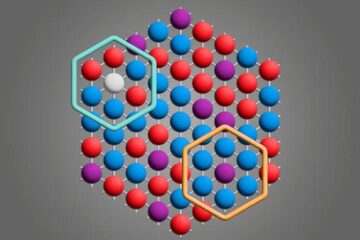
Microscopic basis of a new form of quantum magnetism
Not all magnets are the same. When we think of magnetism, we often think of magnets that stick to a refrigerator’s door. For these types of magnets, the electronic interactions…

An epigenome editing toolkit to dissect the mechanisms of gene regulation
A study from the Hackett group at EMBL Rome led to the development of a powerful epigenetic editing technology, which unlocks the ability to precisely program chromatin modifications. Understanding how…
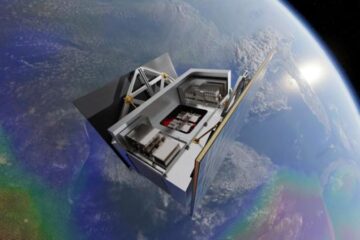
NASA selects UF mission to better track the Earth’s water and ice
NASA has selected a team of University of Florida aerospace engineers to pursue a groundbreaking $12 million mission aimed at improving the way we track changes in Earth’s structures, such…





















