This Article Will Self-destruct: A Tool to Make Online Personal Data Vanish

Computers have made it virtually impossible to leave the past behind. College Facebook posts or pictures can resurface during a job interview. A lost cell phone can expose personal photos or text messages. A legal investigation can subpoena the entire contents of a home or work computer, uncovering incriminating, inconvenient or just embarrassing details from the past.
The University of Washington has developed a way to make such information expire. After a set time period, electronic communications such as e-mail, Facebook posts and chat messages would automatically self-destruct, becoming irretrievable from all Web sites, inboxes, outboxes, backup sites and home computers. Not even the sender could retrieve them.
“If you care about privacy, the Internet today is a very scary place,” said UW computer scientist Tadayoshi Kohno. “If people understood the implications of where and how their e-mail is stored, they might be more careful or not use it as often.”
The team of UW computer scientists developed a prototype system called Vanish that can place a time limit on text uploaded to any Web service through a Web browser. After a set time text written using Vanish will, in essence, self-destruct. A paper about the project went public today and will be presented at the Usenix Security Symposium Aug. 10-14 in Montreal.
Co-authors on the paper are doctoral student Roxana Geambasu, assistant professor Tadayoshi Kohno, professor Hank Levy and undergraduate student Amit Levy, all with the UW's department of computer science and engineering. The research was funded by the National Science Foundation, the Alfred P. Sloan Foundation and Intel Corp.
“When you send out a sensitive e-mail to a few friends you have no idea where that e-mail is going to end up,” Geambasu said. “For instance, your friend could lose her laptop or cell phone, her data could be exposed by malware or a hacker, or a subpoena could require your e-mail service to reveal your messages. If you want to ensure that your message never gets out, how do you do that?”
Many people believe that pressing the “delete” button will make their data go away.
“The reality is that many Web services archive data indefinitely, well after you've pressed delete,” Geambasu said.
Simply encrypting the data can be risky in the long term, the researchers say. The data can be exposed years later, for example, by legal actions that force an individual or company to reveal the encryption key. Current trends in the computing and legal landscapes are making the problem more widespread.
“In today's world, private information is scattered all over the Internet, and we can't control the lifetime of that data,” said Hank Levy. “And as we transition to a future based on cloud computing, where enormous, anonymous datacenters run the vast majority of our applications and store nearly all of our data, we will lose even more control.”
The Vanish prototype washes away data using the natural turnover, called “churn,” on large file-sharing systems known as peer-to-peer networks. For each message that it sends, Vanish creates a secret key, which it never reveals to the user, and then encrypts the message with that key. It then divides the key into dozens of pieces and sprinkles those pieces on random computers that belong to worldwide file-sharing networks, the same ones often used to share music or movie files. The file-sharing system constantly changes as computers join or leave the network, meaning that over time parts of the key become permanently inaccessible. Once enough key parts are lost, the original message can no longer be deciphered.
In the current Vanish prototype, the network's computers purge their memories every eight hours. (An option on Vanish lets users keep their data for any multiple of eight hours.)
Unlike existing commercial encryption services, a message sent using Vanish is kept private by an inherent property of the decentralized file-sharing networks it uses.
“A major advantage of Vanish is that users don't need to trust us, or any service that we provide, to protect or delete the data,” Geambasu says.
Researchers liken using Vanish to writing a message in the sand at low tide, where it can be read for only a few hours before the tide comes in and permanently washes it away. Erasing the data doesn't require any special action by the sender, the recipient or any third party service.
“Our goal was really to come up with a system where, through a property of nature, the message, or the data, disappears,” Hank Levy says.
Vanish was released today as a free, open-source tool that works with the Firefox browser. To work, both the sender and the recipient must have installed the tool. The sender then highlights any sensitive text entered into the browser and presses the “Vanish” button. The tool encrypts the information with a key unknown even to the sender.
That text can be read, for a limited time only, when the recipient highlights the text and presses the “Vanish” button to unscramble it. After eight hours the message will be impossible to unscramble and will remain gibberish forever.
Vanish works with any text entered into a Web browser: Web-based e-mail such as Hotmail, Yahoo and Gmail, Web chat, or the social networking sites MySpace and Facebook. The Vanish prototype now works only for text, but researchers said the same technique could work for any type of data, such as digital photos.
It is technically possible to save information sent with Vanish. A recipient could print e-mail and save it, or cut and paste unencrypted text into a word-processing document, or photograph an unscrambled message. Vanish is meant to protect communication between two trusted parties, researchers say.
“Today many people pick up the phone when they want to talk with a lawyer or have a private conversation,” Kohno said. “But more and more communication is happening online. Vanish is designed to give people the same privacy for e-mail and the Web that they expect for a phone conversation.”
For more information, contact Geambasu at 206-685-1963 or roxana@cs.washington.edu, Hank Levy at 206-543-9204 or levy@cs.washington.edu, and Kohno at 206-331-0840 or yoshi@cs.washington.edu. On Tuesday and Wednesday Kohno will be in Boston and best reached via e-mail.
Media Contact
More Information:
http://vanish.cs.washington.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
Targeted use of enfortumab vedotin for the treatment of advanced urothelial carcinoma
New study identifies NECTIN4 amplification as a promising biomarker – Under the leadership of PD Dr. Niklas Klümper, Assistant Physician at the Department of Urology at the University Hospital Bonn…
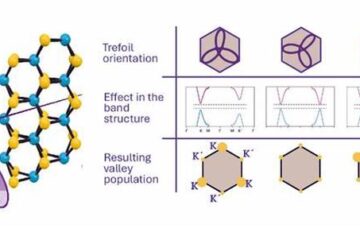
A novel universal light-based technique
…to control valley polarization in bulk materials. An international team of researchers reports in Nature a new method that achieves valley polarization in centrosymmetric bulk materials in a non-material-specific way…
How evolution has optimised the magnetic sensor in birds
The magnetic sense of migratory birds is probably based on the protein cryptochrome 4, and a genetic study has now provided further support for this theory. A team of researchers…





















