Better protection against cyber-attacks

Professor Jürgen Schönwälder heads the Jacobs University’s research group on cybersecurity Jacobs University
We have a growing number of devices around us in our everyday life that contain small embedded computer systems. Many of these devices are able to access the Internet. They can be found in modern cars, in the medical health system, or in our “smart” homes.
Using voice-control systems like Alexa to change settings of smart light-bulbs or other electric devices is getting popular. It is meanwhile possible to buy smart light-bulbs for 15 euros that have an embedded computer system and that are able to access the Internet via the wireless home network in order to be managed by voice-control systems like Alexa.
While this technology enables entirely new ways of interaction with our environment, there are several important security issues that need to be taken care of. A light-bulb accessing a home network, for example, will store credentials (e.g. a password) that are needed to access the home network.
Is this data stored in such a way that it remains protected even when the light-bulb is decommissioned or sold over eBay? Or is this information perhaps even communicated to online cloud services the user may not be aware of? With whom is the light-bulb allowed to communicate in general? Is the software on the light-bulb static or does it enable updates to fix security flaws? If it supports software updates, how does the light bulb make sure that the new software is from a trusted source?
A general underlying question is how can we ensure that the software running on embedded devices is the software that is expected to run on these devices (and not modified by third parties to index, for example, the photo collection accessible on your home network). Finding answers to these questions is a goal of the research undertaken at Jacobs University as part of the CONCORDIA project.
Further questions can be addressed to:
Jürgen Schönwälder | Professor of Computer Science
j.schoenwaelder@jacobs-university.de | Tel.: +49 421 200-3587
Further information:
https://www.concordia-h2020.eu/
Media Contact
More Information:
http://www.jacobs-university.de/All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
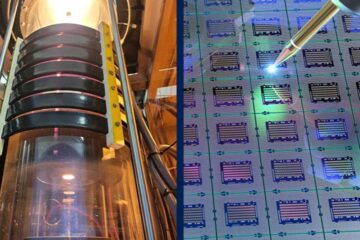
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
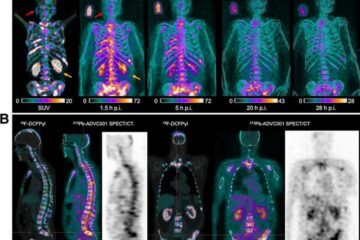
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















