NIST wants comments on proposed 'hash' competition

As a first step in this process, NIST is looking for comments on its recently published draft minimum acceptability requirements, submission requirements and evaluation criteria for candidate algorithms.
Hashing algorithms are mathematical procedures that take data, usually a message, and chop and combine it down into a much shorter number that is a “fingerprint” of the original data. Good hash algorithms have two features—two different inputs are overwhelmingly likely to generate two different fingerprints, and given a specific fingerprint, there is no practical way of calculating a set of input data that will have the same fingerprint.
Hash algorithms are used widely by the federal government and others in various applications, such as digital signatures and message authentication. FIPS 180-2 specifies five cryptographic hash algorithms—SHA-1, SHA-224, SHA-256, SHA-384 and SHA-512. Because serious attacks have been reported in recent years against cryptographic hash algorithms, including SHA-1, NIST is preparing the groundwork for a more secure hash standard.
Media Contact
More Information:
http://www.nist.govAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
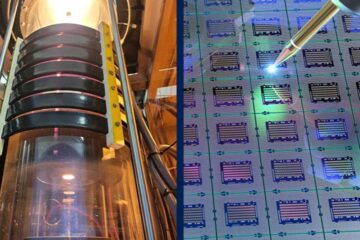
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
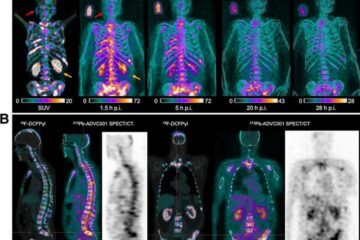
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















