Thwarting ’stealth attacks’ a wireless security must

The profusion of wireless communications in homes, in coffee shops and even on battlefields presents us with fantastic new conveniences — but also new security problems. Indiana University computer scientist Markus Jakobsson will discuss “stealth” attacks over wireless networks, which can disrupt communications and endanger personal information. One such attack is “denial of service,” in which devices are overloaded with so much incoming information they cease functioning properly.
Jakobsson will also discuss “man in the middle” attacks, in which a miscreant invisibly inserts himself into the communication path of two wireless devices, such as cell phones, PDAs, or wireless-enabled laptop computers.
By manipulating software protocols, a man-in-the-middle attacker can silently pass information between two legitimate points while listening in to the wireless conversation, gleaning sensitive personal information or just plain sabotaging the connection. Stealth attacks over wireless networks threaten the security of personal information, online banking and purchasing. Such attacks may also endanger military personnel, who increasingly rely on wireless communications for maneuvering orders and reconnaissance. Defending against stealth attacks in the civilian sector, Jakobsson argues, will require a concerted effort to develop and distribute new software.
Jakobsson is an associate director of the IU Center for Applied Cybersecurity Research and an associate professor in IU’s School of Informatics. A stealth attack FAQ written by Jakobsson is here: http://www.stealth-attacks.info/.
“Stealth Attacks on Wireless Networks”
Saturday, February 19, 9:45 – 11:15 a.m.
Jakobsson and colleagues will present new findings and position statements on Internet security during a press conference on Saturday, Feb. 19, at 8:30 a.m. in the Marriott Wardman Park Hotel’s Taft Room.
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Superradiant atoms could push the boundaries of how precisely time can be measured
Superradiant atoms can help us measure time more precisely than ever. In a new study, researchers from the University of Copenhagen present a new method for measuring the time interval,…
Ion thermoelectric conversion devices for near room temperature
The electrode sheet of the thermoelectric device consists of ionic hydrogel, which is sandwiched between the electrodes to form, and the Prussian blue on the electrode undergoes a redox reaction…
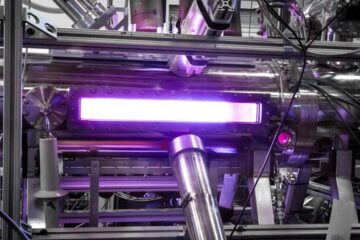
Zap Energy achieves 37-million-degree temperatures in a compact device
New publication reports record electron temperatures for a small-scale, sheared-flow-stabilized Z-pinch fusion device. In the nine decades since humans first produced fusion reactions, only a few fusion technologies have demonstrated…





















