Researchers create next-generation software to identify complex cyber network attacks

By their very nature networks are highly interdependent and each machine’s overall susceptibility to attack depends on the vulnerabilities of the other machines in the network. Attackers can take advantage of multiple vulnerabilities in unexpected ways, allowing them to incrementally penetrate a network and compromise critical systems. In order to protect an organization’s networks, it is necessary to understand not only individual system vulnerabilities, but also their interdependencies.
“Currently, network administrators must rely on labor-intensive processes for tracking network configurations and vulnerabilities, which requires a great deal of expertise and is error prone because of the complexity, volume and frequent changes in security data and network configurations,” says Sushil Jajodia, university professor and director of the Center for Secure Information Systems. “This new software is an automated tool that can analyze and visualize vulnerabilities and attack paths, encouraging ‘what-if analysis’.”
The software developed at Mason, CAULDRON, allows for the transformation of raw security data into roadmaps that allow users to proactively prepare for attacks, manage vulnerability risks and have real-time situational awareness. CAULDRON provides informed risk analysis, analyzes vulnerability dependencies and shows all possible attack paths into a network. In this way, it accounts for sophisticated attack strategies that may penetrate an organization’s layered defenses.
CAULDRON’s intelligent analysis engine reasons through attack dependencies, producing a map of all vulnerability paths that are then organized as an attack graph that conveys the impact of combined vulnerabilities on overall security. To manage attack graph complexity, CAULDRON includes hierarchical graph visualizations with high-level overviews and detail drilldown, allowing users to navigate into a selected part of the big picture to get more information.
“One example of this software in use is at the Federal Aviation Administration. They recently installed CAULDRON in their Cyber Security Incident Response Center and it is helping them prioritize security problems, reveal unseen attack paths and protect across large numbers of attack paths,” says Jajodia. “While currently being used by the FAA and defense community, the software is applicable in almost any industry or organization with a network and resources they want to keep protected, such as banking or education.”
Funding for this software development was provided by the defense, homeland security and intelligence communities, the FAA and Mason. Researchers in the Center for Secure Information Systems involved in the software development include Jajodia; Steven Noel, associate director; and Pramod Kalapa, senior research scientist.
About The Center for Secure Information Systems
Housed in the Volgenau School of Information Technology and Engineering, the Center for Secure Information Systems (CSIS) was established in 1990, as the first academic center in security at a U.S. university. One of the nation’s premier security research organizations, it is also a charter NSA Center of Academic Excellence in Information Assurance Education. CSIS maintains a dedicated full-time team of scientists and engineers with a wide range of expertise, including vulnerability analysis, network attack modeling, intrusion detection, penetration testing and related areas. The range and depth of experience of CSIS team members allows the center to understand and anticipate client requirements, and to formulate innovative solutions and build high-quality tools to meet those requirements.
About George Mason University
George Mason University, located in the heart of Northern Virginia’s technology corridor near Washington, D.C., is an innovative, entrepreneurial institution with national distinction in a range of academic fields. With strong undergraduate and graduate degree programs in engineering, information technology, biotechnology and health care, Mason prepares its students to succeed in the work force and meet the needs of the region and the world. Mason professors conduct groundbreaking research in areas such as cancer, climate change, information technology and the biosciences, and Mason’s Center for the Arts brings world-renowned artists, musicians and actors to its stage. Its School of Law is recognized by U.S. News & World Report as one of the top 35 law schools in the United States.
Media Contact
More Information:
http://www.gmu.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Properties of new materials for microchips
… can now be measured well. Reseachers of Delft University of Technology demonstrated measuring performance properties of ultrathin silicon membranes. Making ever smaller and more powerful chips requires new ultrathin…

Floating solar’s potential
… to support sustainable development by addressing climate, water, and energy goals holistically. A new study published this week in Nature Energy raises the potential for floating solar photovoltaics (FPV)…
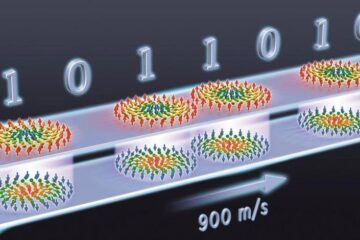
Skyrmions move at record speeds
… a step towards the computing of the future. An international research team led by scientists from the CNRS1 has discovered that the magnetic nanobubbles2 known as skyrmions can be…





















