Me, myself and I: manage online identity more safely

Strangers can build a fairly complete picture of our movements, transactions and relationships from the cyber-trail we leave behind. This has major implications for what has become a pervasive tool to society, business and administrations.
Privacy and identity management are fast becoming fundamental to future developments on the internet. Hard-won trust in e-commerce and in using e-government services, for example, could quickly erode if security issues are not properly addressed.
Two basic rules govern how people can better protect themselves online, according to specialists. First, we need to “separate contexts” so that observers cannot accumulate sensitive data – basically, by making it much harder for cyber-spies to join the online dots of our lives. Second, and crucially, we have to really keep track of what we do disclose.
These rules form the basis of the concepts and prototypes developed within the PRIME project. Perhaps borrowing from the Joan Armatrading song, PRIME’s mantra is “Me, myself and I! Manage your identities safely”.
“Our main aim is for people to gain autonomy over their personal data, so they can make informed decisions on what information they provide online,” says project partner Marit Hansen of Germany’s Independent Centre for Privacy Protection (ULD, the Data Protection Authority for Land Schleswig-Holstein).
Like a good poker player who never fully reveals his hand, good identity management (IDM) means choosing and developing appropriate partial identities. For example, OnionCoffee is a PRIME software module written in Java to help end-users exchange information anonymously over the internet.
Disclosure, not exposure
It is a bit of a balancing act. To get the most from online services, we often have to disclose more about ourselves, but can we do it without unnecessary exposure? PRIME thinks we can.
The EU-funded project has put together a toolbox, console (interface for managing identity online) and middleware (software to glue components together) to help individuals and organisations wrest control of their online identities.
The toolbox or building blocks make good use of tutorials, application modules and documentation, including a White Paper published in 2007. The tools PRIME developed marry the need for accountability (i.e. proving you are 18 to enter certain websites) with the need for anonymity.
A key component is the use of “private credentials” derived from certificates issued by, say, professional ID providers, such as online payment operators, on different pseudonyms for the same person.
“Multiple private credentials can be created from a single certificate,” says Hansen. Using cryptography, there is nothing tying them so the person's anonymity is assured. If the system is abused – i.e. fraudulent and/or antisocial behaviour – the anonymity built into the private credentials can be revoked, and appropriate action taken against the individual, she warns.
Sticky policies
Better-designed websites and workflows, separating different tasks and corresponding databases, would also help protect users’ privacy, PRIME research suggests. As, too, would a commitment by organisations to enforce their data privacy policies more diligently, and to make them easier for online customers and users to understand and verify before and after transacting.
“Sticky policies” can also be written into IDM applications so that the policy literally travels on the back of the data being transferred. This means, if data is passed on (legally) to third parties, the policy stays with the data, thus protecting the source’s privacy (i.e. that means you and I).
So using a combination of pseudonyms and PRIME private credentials, data provided through e-commerce, e-health, or e-government applications are secured against future misuse. In principle, this also works in web-mail accounts and online social networking, which is one of the extended scenarios dealt with in the follow-up EU-funded project PrimeLife, starting in 2008.
PET project
Another web-based system developed by PRIME also helps us keep track of what we have already put out in cyberspace. The ‘Data Track’ tool in PRIME’s console works like the web-history in your browser, monitoring the ‘what’, ‘to whom’ and ‘when’ of online transactions.
Data Track also records the privacy policies of the service providers, and lets you query how your data has been used after the fact. It also helps you (re)use appropriate accounts – logins and passwords – in different contexts, keeping them apart (unless otherwise instructed).
PRIME has developed its tools and applications in the sprit of the EU’s ‘privacy enhancing technologies’ (PET) initiative. According to the European Commission, wider development and use of PETs should boost efforts to protect citizens’ privacy. The project is also actively engaged in standard setting, such as ISO and W3C, in identity management.
Since 2004, PRIME has pioneered this multiple-context approach to digital IDM, suggests Hansen. Today, as online security concerns have grown, there is an even stronger case for its approach, as well as an untapped market for its components, especially with digital signature providers and mobile data handlers.
“The market is ripe for better data protection and privacy solutions, especially as more mobile data transactions take place, and we are well placed to capitalise on this,” confirms Hansen. “In fact, we’re very interested in commercial or marketing partnerships to make this happen.”
PRIME has already spun-off a location-based service system to Germany’s T-Mobile and plans to refine some of its tools and platforms, particularly in data structuring and workflow, in PrimeLife, which was recently presented at the CISTRANA Topical Seminar on ICT Security.
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
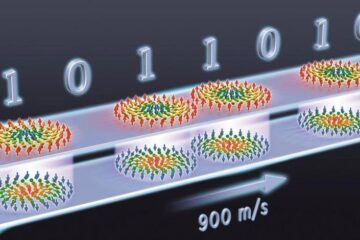
Skyrmions move at record speeds
… a step towards the computing of the future. An international research team led by scientists from the CNRS1 has discovered that the magnetic nanobubbles2 known as skyrmions can be…
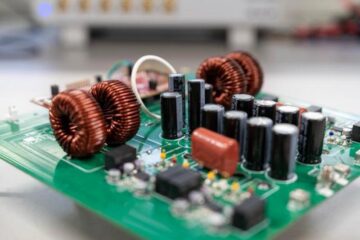
A flexible and efficient DC power converter for sustainable-energy microgrids
A new DC-DC power converter is superior to previous designs and paves the way for more efficient, reliable and sustainable energy storage and conversion solutions. The Kobe University development can…
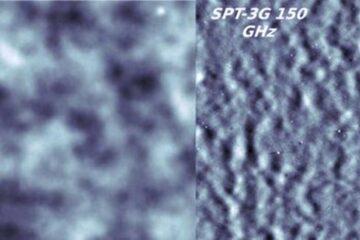
Technical Trials for Easing the (Cosmological) Tension
A new study sorts through models attempting to solve one of the major challenges of contemporary cosmic science, the measurement of its expansion. Thanks to the dizzying growth of cosmic…





















