Georgia Tech Warns of Threats to Cloud Data Storage, Mobile Devices in Latest ‘Emerging Cyber Threats’ Report

These concerns are among findings made by the Georgia Tech Information Security Center (GTISC) and the Georgia Tech Research Institute (GTRI) in today's release of the Georgia Tech Emerging Cyber Threats Report for 2014.
The report was released at the annual Georgia Tech Cyber Security Summit, a gathering of industry and academic leaders who have distinguished themselves in the field of cyber security.
“With recent revelations of data collection by the federal government, we will continue to see a focus on cloud security,” said Wenke Lee, director of GTISC. “But encryption in the cloud often impacts data accessibility and processing speed. So we are likely to see increased debate about the tradeoffs between security, functionality and efficiency.”
Encryption challenges were a focus at this year’s summit, which featured some of the nation’s top information security experts. These included keynote speaker Martin Hellman, professor emeritus at Stanford University and one of the inventors of public key cryptography, a way of securing communications without relying on pre-shared secrets.
In related findings, the report reveals security issues involving the “Internet of Things,” referring to the notion that the increase of Internet-capable devices could create opportunities remote hacking and data leakage. With everything from home automation to smartphones and other personal devices becoming connected to the Internet, these devices will capture more real-world information and could permit outside parties, companies, and governments to misuse that information.
In the mobile space, even though designers of mobile devices and tablets have developed a robust ecosystem to prevent large-scale device compromises, the report finds that the threat of malicious and potentially targeted use remains. Earlier this year, researchers at Georgia Tech reported that they found ways to bypass the vetting process of Apple’s App Store and subsequently showed how malicious USB chargers can be used to infect Apple iOS devices.
“No matter how successful we have been, black hat operatives will continue to attack infrastructure at every angle possible, making cyber security a global issue for years to come,” said Bo Rotoloni, director of GTRI’s Cyber Technology and Information Security Laboratory (CTISL). “We must remain vigilant. The purpose of this Summit and Report is to raise awareness, create educational opportunities and maintain an ongoing dialogue among industry, academia and government.”
The Georgia Tech Cyber Security Summit is a forum for the IT security ecosystem to gather together, discuss and debate the evolving nature of cyber threats, and to chart the course for creating collaborative solutions.
In addition to Hellman’s keynote address, the 2013 Summit included a panel of security experts from Microsoft, Splunk, Dell Secureworks, Solera Networks and Georgia Tech.
The Georgia Institute of Technology is one of the nation's leading public research universities and the home of cyber security research and education initiatives through GTISC, GTRI and other facilities across campus. These efforts focus on producing technology and innovations that help drive economic growth and improve daily life on a global scale.
The report will be available for download at gtsecuritysummit.com.
Media Contact
More Information:
http://www.gatech.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Bringing bio-inspired robots to life
Nebraska researcher Eric Markvicka gets NSF CAREER Award to pursue manufacture of novel materials for soft robotics and stretchable electronics. Engineers are increasingly eager to develop robots that mimic the…

Bella moths use poison to attract mates
Scientists are closer to finding out how. Pyrrolizidine alkaloids are as bitter and toxic as they are hard to pronounce. They’re produced by several different types of plants and are…
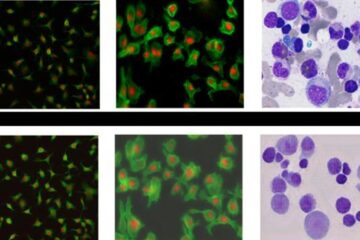
AI tool creates ‘synthetic’ images of cells
…for enhanced microscopy analysis. Observing individual cells through microscopes can reveal a range of important cell biological phenomena that frequently play a role in human diseases, but the process of…





















