Cloud computing: gaps in the “cloud” – Massive security flaws at Amazon Web Services discovered

Researchers from Ruhr-University Bochum have found a massive security gap at Amazon Cloud Services. Using different methods of attack (signature wrapping and cross site scripting) they tested the system which was deemed “safe”.
“Based on our research results, Amazon confirmed the security gaps and closed them immediately”, said Prof. Dr. Jörg Schwenk, chair for network and data security at the RUB. Amazon Web Services (AWS) offers its customers cloud computing services and hosts, among others, services like Twitter, Second Life and 4Square.
Cloud computing could be the major computing paradigm of tomorrow. The idea of processing and storing software and data in a cheap external infrastructure is becoming increasingly popular. The fact that these services are by no means as secure as promised is now demonstrated by the research results of Prof. Schwenk and his staff.
Concentrated computing power
The “Cloud” is a collection of many virtual servers with concentrated computing power. Outsourcing to cloud computing has many advantages for professional users: they can rent storage and server capacity short term on demand. The service is invoiced, for example, according to the usage period, and the customer saves the cost of purchasing his own software and hardware. Up to now, the discussion about cloud computing has above all been dominated by the inability to comply with legal requirements. “Real” attacks were, however, less in the public eye.
Search for weak points
“A major challenge for cloud providers is ensuring the absolute security of the data entrusted to them, which should only be accessible by the clients themselves,” said Prof. Schwenk, who set out with his staff to seek weak points. They have found what they were looking for: Juraj Somorovsky, Mario Heiderich and Meiko Jensen tested the security concept of the cloud provider Amazon Web Services.
XML signature wrapping attacks
“Using different kinds of XML signature wrapping attacks, we succeeded in completely taking over the administrative rights of cloud customers”, said Juraj Somorovsky. “This allowed us to create new instances in the victim’s cloud, add or delete images.” The researchers suspect that many cloud offers are susceptible to signature wrapping attacks, since the relevant web service standards make performance and security incompatible. “We are working on a high-performance solution, however, that no longer has any of the known security gaps”, said Prof. Dr. Jörg Schwenk.
Cross site scripting attacks
In addition, the researchers found gaps in the AWS interface and in the Amazon shop which were ideally suited for smuggling in executable script code – what are termed cross-site scripting attacks. With alarming consequences: “We had free access to all customer data, including authentication data, tokens, and even plain text passwords” said Mario Heiderich. The researcher see the common login as a complex potential danger: “It's a chain reaction. A security gap in the complex Amazon shop always also directly causes a gap in the Amazon cloud.”
Private Clouds also vulnerable
In contrast to public belief, Private Clouds are also vulnerable to the aforementioned attacks: Eucalyptus, an open source project widely used to implement Cloud solutions within companies, did expose the same weaknesses. “A rough classification of cloud technologies cannot replace a thorough security investigation”, states Prof. Schwenk.
Security gaps closed
“Critical services and infrastructures are making increasing use of cloud computing”, explained Juraj Somorovsky. According to industry estimates, the turnover of European cloud services is set to more than double in the next four years – from around 68 billion Euros in 2010 to about 148 billion in 2014. “Therefore it is essential that we recognise the security gaps in cloud computing and avoid them on a permanent basis.” Industry took immediate action: “On our advice, Amazon and Eucalyptus confirmed the security gaps and closed them immediately”.
Further information
Prof. Dr. Jörg Schwenk, Faculty of Electrical Engineering and Information Sciences at the RUB, Chair for Network and Data Security, Tel. +49 234 32 26692
joerg.schwenk@rub.de
Editor: Jens Wylkop
Media Contact
More Information:
http://www.ruhr-uni-bochum.de/All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
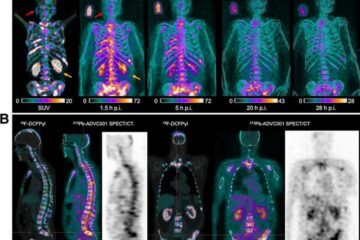
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















