'Control-Alt-Hack' game lets players try their hand at computer security

Now you can at least try, no matter what your background, with a new card game developed by University of Washington computer scientists.
“Control-Alt-Hack” gives teenage and young-adult players a taste of what it means to be a computer-security professional defending against an ever-expanding range of digital threats. The game's creators will present it this week in Las Vegas at Black Hat 2012, an annual information-security meeting.
“Hopefully players will come away thinking differently about computer security,” said creator Yoshi Kohno, a UW associate professor of computer science and engineering.
Players assume the roles of characters with their own special skills. Game play involves completing missions by rolling the dice, using skills and occasionally pulling something out of a bag of tricks.
The target audience is 15- to 30-year-olds with some knowledge of computer science, though not necessarily of computer security. The game could supplement a high school or introductory college-level computer science course, Kohno said, or it could appeal to information technology professionals who may not follow the evolution of computer security.
In the game, players work for Hackers Inc., a small company that performs security audits and consultations for a fee. Three to six players take turns choosing a card that presents a hacking challenge that ranges in difficulty and level of seriousness.
In one mission, a player on a business trip gets bored and hacks the hotel minibar to disrupt its radio-tag payment system, then tells the manager. (A real project being presented at Black Hat this year exposes a security hole in hotel keycard systems.)
“We went out of our way to incorporate humor,” said co-creator Tamara Denning, a UW doctoral student in computer science and engineering. “We wanted it to be based in reality, but more importantly we want it to be fun for the players.”
This is not an educational game that tries to teach something specific, Denning said, but a game that's mainly designed to be fun and contains some real content as a side benefit. The team decided on an old-fashioned tabletop card game to make it social and encourage interaction.
Some scenarios incorporate research from Kohno's Security and Privacy Research Lab, such as security threats to cars, toy robots and implanted medical devices. The missions also touch other hot topics in computer security, such as botnets that use hundreds of hijacked computers to send spam, and vulnerabilities in online medical records.
Characters have various skills they can deploy. In addition to the predictable “software wizardry,” skills include “lock picking” (for instance, breaking into a locked server room) and “social engineering” (like tricking somebody into revealing a password).
Graduate students who are current or former members of the UW lab served as loose models for many of the game's characters. Cards depict the characters doing hobbies, such as motorcycling and rock climbing, that their real-life models enjoy.
“We wanted to dispel people's stereotypes about what it means to be a computer scientist,” Denning said.
The UW group licensed the game's mechanics from award-winning game designer Steve Jackson of Austin, Texas. The group hired an artist to draw the characters and a Seattle firm to design the graphics. Adam Shostack, a security professional who helped develop a card game at Microsoft in 2010, is a collaborator and co-author.
Intel Corp. funded the game as a way to promote a broader awareness of computer-security issues among future computer scientists and current technology professionals. Additional funding came from the National Science Foundation and the Association for Computing Machinery's Special Interest Group on Computer Science Education.
Educators in the continental U.S. can apply to get a free copy of the game while supplies last. It's scheduled to go on sale in the fall for a retail price of about $30.
For more information about the project, contact Kohno at yoshi@cs.washington.edu and Denning at tdenning@cs.washington.edu.
For more information about the game, visit the website at www.controlalthack.com or email info@controlalthack.com
Media Contact
More Information:
http://www.uw.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
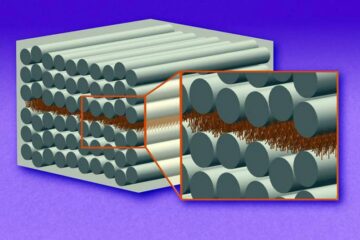
“Nanostitches” enable lighter and tougher composite materials
In research that may lead to next-generation airplanes and spacecraft, MIT engineers used carbon nanotubes to prevent cracking in multilayered composites. To save on fuel and reduce aircraft emissions, engineers…

Trash to treasure
Researchers turn metal waste into catalyst for hydrogen. Scientists have found a way to transform metal waste into a highly efficient catalyst to make hydrogen from water, a discovery that…
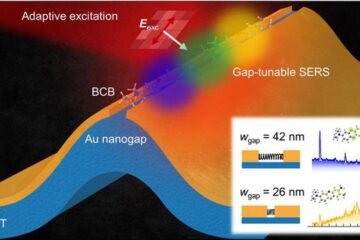
Real-time detection of infectious disease viruses
… by searching for molecular fingerprinting. A research team consisting of Professor Kyoung-Duck Park and Taeyoung Moon and Huitae Joo, PhD candidates, from the Department of Physics at Pohang University…





















