Disposable credit card numbers

Writing in a recent issue of the Inderscience publication International Journal of Electronic Security and Digital Forensics Mohammed Assora, James Kadirire and Ayoub Shirvani explain how a disposable credit card number would protect consumers from fraud when shopping online.
Today, e-commerce transactions are performed by sending the customer's credit card details over the Internet between a web browser and the e-commerce site. Despite rudimentary security, there are many points at which the process can be compromised by a fraudster.
The most insecure aspect of the whole process, explains Shirvani and colleagues, is the client authentication step because most e-commerce sites usually only require the customer's credit card details to validate the sale. There is no certification on the customer's side of the bargain. This means that anyone who steals your credit card information could use it to buy goods and services online fraudulently.
Customer certification is not the only problem, the researchers say. Once you have entered your credit card details into a shopping or other e-commerce site, these are usually stored unencrypted in the merchant’s database, which means they could be retrieved by anyone with access to that database, whether or not that is an unscrupulous employee or someone breaking in to the database from outside.
The researchers point out that more than a decade has passed since computer security experts instigated the Secure Electronic Transaction
(SET) protocol to try to solve this problem by sending the client's credit card details encrypted. However, the system was very complicated and has not been adopted by e-commerce sites.
Instead, Shirvani and colleagues put forward the idea of a disposable credit card number (DCCN) that could overcome the vast majority of security threats. They describe how DCCNs could be generated “off-line” using a pre-shared secret key between the issuer and the customer and used only once to make an electronic purchase.
The concept is related to the credit voucher and gift certificate systems used by some e-commerce sites but the off-line system means no credit card details need pass across the Internet to create the voucher code. The off-line approach would also side-step any potential security and implementation issues that might be associated with online DCCNs such as Private Payment and SecureClick.
In off-line generation of DCCNs, the customer registers his/her credit card with the card issuer and receives an associated secret key. The customer will then use this secret key in conjunction with a simple calculation device such as a smart card, PDA or mobile phone to generate an encrypted code – known as a hash – that is based on the price of the goods he/she intends to purchase and other details pertinent to the e-commerce site.
The resulting hash is adapted to form the DCCN, and then sent over the Internet instead of the actual credit card details. The shopping site validates the DCCN as any normal credit card without ever seeing or having to store their real credit card details. As a result, the client can shop with no need to worry about confidential data being compromised, the researchers conclude.
Media Contact
All latest news from the category: Business and Finance
This area provides up-to-date and interesting developments from the world of business, economics and finance.
A wealth of information is available on topics ranging from stock markets, consumer climate, labor market policies, bond markets, foreign trade and interest rate trends to stock exchange news and economic forecasts.
Newest articles
High-energy-density aqueous battery based on halogen multi-electron transfer
Traditional non-aqueous lithium-ion batteries have a high energy density, but their safety is compromised due to the flammable organic electrolytes they utilize. Aqueous batteries use water as the solvent for…

First-ever combined heart pump and pig kidney transplant
…gives new hope to patient with terminal illness. Surgeons at NYU Langone Health performed the first-ever combined mechanical heart pump and gene-edited pig kidney transplant surgery in a 54-year-old woman…
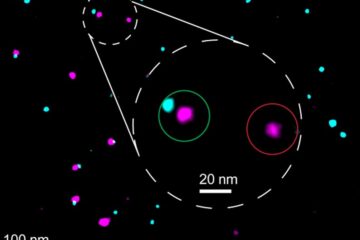
Biophysics: Testing how well biomarkers work
LMU researchers have developed a method to determine how reliably target proteins can be labeled using super-resolution fluorescence microscopy. Modern microscopy techniques make it possible to examine the inner workings…





















