New forensic technique gives clues about sharks from bite damage

In a method analogous to analyzing human fingerprints, scientists can make identifications by precisely comparing shark bites to the jaws and teeth of the powerful predators, said George Burgess, director of the International Shark Attack File, which is housed at UF’s Florida Museum of Natural History.
“Every time we investigate a shark attack one of the pieces of information that we want to have is what species was involved and what size it was,” he said. “Because I’ve been looking at shark attack victims for 30 years I can estimate what did the damage, but I have never been able to actually prove it.”
Now scientists can say with a degree of certainty whether the beast was a 14-foot tiger shark or a 9-foot bull shark, a distinction that has unforeseen emotional, ecological and even monetary benefits, said Burgess, who collaborated with researchers from the University of South Florida. Their findings are published in the November issue of Marine Biology.
“There’s a psychological need for many shark attack victims to know what bit them,” Burgess said. “One of the few things shark attack victims have going for them after a bite is bragging rights and the bragging rights include knowing what did the damage.”
Because of the hype surrounding shark attacks, off-the-cuff estimates of shark size are often exaggerated, he said. “This will give an actual basis for determining what species was involved and the size, not that that’s going to affect the size claimed by the victim in a bar,” he said.
Using dried shark jaws from museums and private collections, the researchers were able to identify bite patterns of particular sizes and species of sharks by measuring jaw circumference and the distance between the six frontal teeth on the top and lower jaws, Burgess said. They experimented on 10 to 24 sets of shark jaws for each of the 14 species they analyzed. The technique works not only on human and animal tissue, but also on inanimate objects like surfboards and underground cable lines, he said.
The ability to make predictions from bite patterns is important to understanding the behavioral underpinnings of shark attacks and their prey habits, said lead researcher Dayv Lowry, a biologist with the Washington Department of Fish and Wildlife, who did the work as a graduate student at the University of South Florida.
“Often someone will send us a picture of a dolphin carcass or a sea turtle and want to know what kind of shark bit it,” Lowry said. “Knowing that it’s a large tiger shark, for example, would help us figure out what large tiger sharks like to eat and how they attack their prey. If an animal or person has been bitten on the rear end, then we know these sharks are likely to sneak up to get their prey instead of facing the victims.”
Being able to determine what size shark attacked people in certain geographic areas such as South Africa where offshore nets are used to protect swimmers is valuable because it may influence the size mesh that is used, Lowry said. With larger sharks, beaches can get by with bigger mesh sizes, which are cheaper and less environmentally intrusive, he said.
The technique also has the potential to save thousands of dollars in damages caused by the sharks’ penchant for attacking underwater electronic equipment, which includes intercontinental telephone wires, top-secret communication lines between government officials and sensors companies use to uncover oil fields, Burgess said.
Sharks are equipped with organs on the underside of their snouts – gel filled pits called ampullae of Lorenzini – that allow them to detect electromagnetic fields from their intended food, Burgess said. Unfortunately, sharks often do not distinguish between the signals sent by prey and equipment, which can be ruined by water seeping in through the bite marks, he said.
“That’s one thing that makes them special — they can sense electro-magnetic fields around their prey items,” he said.
Laying cable lines at the bottom of the ocean is extremely expensive, and having to remove a piece, fix it and install it again adds to the cost, Burgess said. “Knowing that a certain species of shark did the damage is useful because in the future cable lines can be placed in a different location, outside the path of that particular shark’s area of distribution,” he said.
And the ability to determine what size shark was involved in an attack by the size and configuration of its bite marks could result in the installation of a heavier seal designed to withstand damage from that kind of shark, he said.
Credits
Writer
Cathy Keen, ckeen@ufl.edu, 352-392-0186
Source
George Burgess, gburgess@flmnh.ufl.edu, 352-392-2360
Media Contact
More Information:
http://www.ufl.eduAll latest news from the category: Life Sciences and Chemistry
Articles and reports from the Life Sciences and chemistry area deal with applied and basic research into modern biology, chemistry and human medicine.
Valuable information can be found on a range of life sciences fields including bacteriology, biochemistry, bionics, bioinformatics, biophysics, biotechnology, genetics, geobotany, human biology, marine biology, microbiology, molecular biology, cellular biology, zoology, bioinorganic chemistry, microchemistry and environmental chemistry.
Newest articles
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
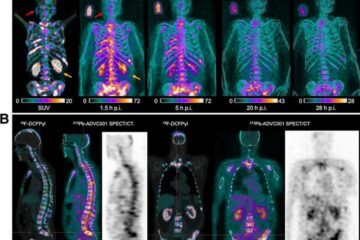
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















