Researchers uncover online auction fraud

The new method analyzes publicly available histories of transactions posted by online auction sites such as eBay and identifies suspicious online behaviors and dubious associations among users.
Online auction sites are immensely popular. The largest, eBay, reported third quarter revenues of $1.449 billion, up 31 percent from the previous year, and registered 212 million users, up 26 percent. But the popularity of online auction sites also makes them a target for crooks. Internet auction fraud, such as failure to deliver goods after a sale, accounted for almost two-thirds of the 97,000 complaints referred to law enforcement agencies last year by the federal Internet Crime Complaint Center.
Perpetrators of these frauds have distinctive online behaviors that cause them to be readily purged from an online auction site, said Computer Science Professor Christos Faloutsos. The software developed by his research team — Network Detection via Propagation of Beliefs, or NetProbe — could prevent future frauds by identifying their accomplices, who can lurk on a site indefinitely and enable new generations of fraudsters.
In a test analysis of about one million transactions between almost 66,000 eBay users, NetProbe correctly detected 10 previously identified perpetrators, as well as more than a dozen probable fraudsters and several dozen apparent accomplices.
“To the best of our knowledge, this is the first work that uses a systematic approach to analyze and detect electronic auction frauds,” said Faloutsos, who noted that NetProbe could eventually be useful for both law enforcement and security personnel of online sites.
The researchers have already adapted the software to provide a trustworthiness score for individual user IDs. Though not yet available to the public, the NetProbe score would complement user reputation scores that many auction sites already provide to help prevent fraud.
“We want to help people detect potential fraud before the fraud occurs,” said research associate Duen Horng “Polo” Chau, who developed NetProbe with Faloutsos, undergraduate student Samuel Wang and graduate student Shashank Pandit.
Many auction sites try to avert fraud with so-called reputation systems. In eBay's case, buyers can report whether they had a positive, neutral or negative experience in a transaction, and that report is then translated into a feedback score for that seller.
Unfortunately, a crook can manipulate these feedback scores, obtaining a favorable score by engaging in a number of legitimate sales. But that is costly and time-consuming and, once the fraudster starts cheating buyers, that user identification is quickly red-flagged and shut down.
Perpetrating frauds may be sustainable, however, if a fraudster has accomplices or sets up separate user IDs to serve as accomplices. These accomplice accounts conduct legitimate transactions and maintain good reputations. They also have many transactions with the user IDs of fraudsters, using their good reputations to boost the fraudsters' feedback scores. Because accomplices don't perpetrate frauds, they usually escape notice and can keep working to establish new fraudster accounts, Faloutsos said.
But an unnatural pattern becomes evident when the transactions are plotted as a graph, with each user represented as a node, or dot, and transactions between individual users represented by lines connecting the nodes.
In the resulting graph, transactions between accomplices and fraudsters create a pattern that sticks out like “a guiding light,” Chau said. Graph theorists call this pattern a “bipartite core” — members of one group have lots of transactions with members of a second group, but don't have transactions with members of their own group. One group, the accomplices, also deals with honest eBay users, but most of the transactions are with fraudster groups.
The researchers tested their method, in part, by accumulating transaction histories from eBay and demonstrating that they could detect the distinctive fraud patterns within these massive data sets. Chau reported on an analysis involving about 100 eBay users at a September data mining conference in Berlin. The team has since analyzed about a million transactions between almost 66,000 eBay users, and those as-yet unpublished findings have been submitted for presentation at an upcoming scientific conference.
“Crooks are extremely ingenious,” Faloutsos warned, so identifying accomplices would not eliminate all online auction fraud. But eliminating accomplices would force crooks to resort to more sophisticated, complex schemes. “These schemes will require more effort and cost, so fraud would be increasingly unprofitable,” he added.
Media Contact
More Information:
http://www.cmu.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
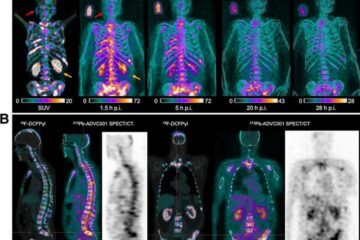
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















