New cyber security protocol for online banking, and more

A new security approach could improve safeguarding of credit card numbers, bank passwords and other sensitive information for those who surf the Internet using wireless connections, researchers told the annual meeting of the American Association for the Advancement of Science (AAAS)on Saturday.
The same protocol could be employed in many computer networks in which two computers, hand-held communication devices or network nodes need to simultaneously verify the identity of each other.
The protocol – called “delayed password disclosure” – was created by Markus Jakobsson and Steve Myers of Indiana University. It may have application in any environment where “mutual identity authentication” is required, the researchers say.
This new security protocol could help to prevent consumers from getting tricked into connecting to a fake wireless hub at an airport, for example. Or the protocol could notify you that the link included in a legitimate-looking e-mail points to a fake website set up to steal your sensitive information, such as passwords and PINs to bank accounts, credit cards numbers and account numbers for online fund-transfer services.
The safety measures also might help stop organized crime and terrorist-funding groups from collecting large numbers of fund-transfer account numbers that could be used for money laundering, the researchers say.
In one possible application, the security protocol could be used to verify that two wireless devices trying to connect to each other don’t mistakenly connect to another device. This is useful to safeguard communications between mobile units, such as between members of emergency crews who are connected through wireless networks built “on the fly.”
These so-called “ad hoc” networks hold great potential for military and emergency response applications where network infrastructures have been destroyed or are nonexistent. The flexibility of ad hoc networks, however, opens the door to attack. The new protocol is meant to strengthen such networks, using a type of electronic “interrogation” to ensure they are not compromised.
The protocol also holds promise as on-line banking becomes more prevalent. In one scenario, criminals could “sift” or launder money through a large number of accounts once the system is compromised by an attacker. Each account would maintain the correct balance for the unsuspecting victim, even as the attacker funneled funds through it. If large numbers of accounts are used, and the payment patterns are intricate, then such misbehavior is difficult to trace to the attacker – who might be working for the payer, the final recipient of the funds, or both.
For network attackers to launder money through online fund-transfer accounts of unsuspecting individuals, the criminals must stop email notifications from the fund-transfer company to the account holder. “Denial of service attacks” and other kinds of network attacks could be employed to stop such notification emails, the researchers say. But spotting such maneuvers is not easy.
“It’s difficult to say exactly what tactics network attackers are using right now because many people do not know they are being attacked. Nonetheless, criminals who have no greater passion than money laundering are already intensely thinking about these kinds of projects,” Jakobsson explained.
The use of delayed password disclosure or a comparable protocol could help to prevent such crimes. If the protocol were used by an online bank, a technical version of the following dialogue would occur between the bank and the online customer to authenticate the identity of both parties without divulging passwords.
CUSTOMER: Hello bank. I know my banking password. If you really are my bank, then you already know my password. I don’t trust you and you don’t trust me. I’m not going to tell you my password. We’re going to use this authentication protocol called “delayed password disclosure.” It allows us to both be sure the other one is not lying about our identity, but without giving out any sensitive information in the process.
BANK: Proceed.
CUSTOMER: Bank, I will send you some information that is encrypted. You can only decrypt it if you know my password. If you don’t know the password, you could of course try all possible passwords (although that is a lot of work!), but you would never know from my message if you picked the right one. Once you have decrypted the message, I want you to send it to me. If it is correctly decrypted, I will know that you know my password already. Once I know that you know my password, I will send it to you so that you can verify that I also know it. Of course, if I am lying about my identity and don’t know the password in the first place, then I will not learn anything about the password from your message, so it is safe in both directions.
For more details on the delayed password disclosure protocol, (patent pending) see the technical document from Markus Jakobsson entitled “Stealth Attacks” which is available at www.stealth-attacks.info
Jakobsson is hoping to have “beta code” for Windows and Mac in spring 2005, and code for common cell phone platforms later in 2005.
MEDIA NOTE: A news briefing on this research will take place at 8:30 a.m. Eastern Time, Saturday, 19 February, during the AAAS Annual Meeting in Washington, DC, in Wilson A of the Marriott Wardman Park Hotel. During the briefing, symposium moderator Susanne Wetzel will set up an ad hoc wireless network and then attack it using a denial of service method. She will show how an “evil node” in the network can quickly drain the battery of a personal digital assistant (PDA). Further, these and other speakers will take part in a symposium titled, “Attacks on and Security Measures for Ad Hoc Wireless Networks,” set to take place Saturday at 9:45 a.m. in the Omni Shoreham Hotel, Level 2B, Empire.
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
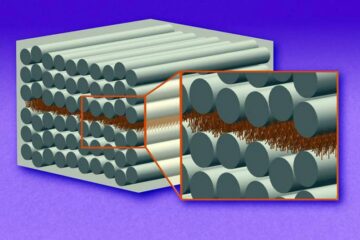
“Nanostitches” enable lighter and tougher composite materials
In research that may lead to next-generation airplanes and spacecraft, MIT engineers used carbon nanotubes to prevent cracking in multilayered composites. To save on fuel and reduce aircraft emissions, engineers…

Trash to treasure
Researchers turn metal waste into catalyst for hydrogen. Scientists have found a way to transform metal waste into a highly efficient catalyst to make hydrogen from water, a discovery that…
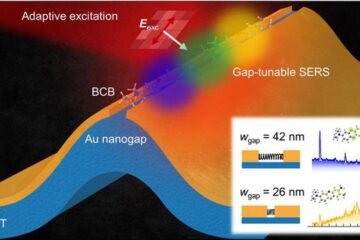
Real-time detection of infectious disease viruses
… by searching for molecular fingerprinting. A research team consisting of Professor Kyoung-Duck Park and Taeyoung Moon and Huitae Joo, PhD candidates, from the Department of Physics at Pohang University…





















