Location spoofing possible with WiFi devices

In January, Skyhook Wireless Inc. announced that Apple would use Skyhook’s WiFi Positioning System (WPS) for its popular Map applications. The WPS database contains information on access points throughout the world. Skyhook itself provides most of the data in the database, with users contributing via direct entries to the database, and requests for localization. ETH Zurich Professor Srdjan Capkun of the Department of Computer Science and his team of researchers analysed the security of Skyhook’s positioning system. The team’s results demonstrate the vulnerability of Skyhook’s and similar public WLAN positioning systems to location spoofing attacks.
Impersonation and elimination
When an Apple iPod or iPhone wants to find its position, it detects its neighbouring access points, and sends this information to Skyhook servers. The servers then return the access point locations to the device. Based on this data, the device computes its location. To attack this localization process, Professor Capkun’s team decided to use a dual approach. First, access points from a known remote location were impersonated. Second, signals sent by access points in the vicinity were eliminated by jamming. These actions created the illusion in localized devices that their locations were different from their actual physical locations.
Simple falsification
Skyhook’s WPS works by requiring a device to report the Media Access Control (MAC) addresses that it detects. However, since MAC addresses can be forged by rogue access points, they can be easily impersonated. Furthermore, access point signals can be jammed and signals from access points in the vicinity of the device can thus be eliminated. These two actions make location spoofing attacks possible.
Compromised usage
Professor Capkun explained that by demonstrating these attacks, the team hoped to point out the limitations, despite guarantees, of public WLAN-based localization services as well as of applications for such services. He said «Given the relative simplicity of the performed attacks, it is clear that the use of WLAN-based public localization systems, such as Skyhook’s WPS, should be restricted in security and safety-critical applications.»
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Bringing bio-inspired robots to life
Nebraska researcher Eric Markvicka gets NSF CAREER Award to pursue manufacture of novel materials for soft robotics and stretchable electronics. Engineers are increasingly eager to develop robots that mimic the…

Bella moths use poison to attract mates
Scientists are closer to finding out how. Pyrrolizidine alkaloids are as bitter and toxic as they are hard to pronounce. They’re produced by several different types of plants and are…
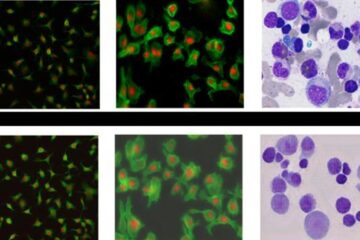
AI tool creates ‘synthetic’ images of cells
…for enhanced microscopy analysis. Observing individual cells through microscopes can reveal a range of important cell biological phenomena that frequently play a role in human diseases, but the process of…





















