Nomadic devices, the freedom to compute

There was a simpler time when a telephone was just a phone, and all you could do with it was call people. Nowadays, mobile phones come packed with more processing juice than a small country possessed not so long ago.
“If you go and buy a phone today, you will find it has more computing power than a PC in the late 1980s and even 1990s. But if you look at the third-party software available on the average mobile, it is almost non existent,” explains Fabio Massacci, a professor in security and computer engineering at the University of Trento in Italy.
“This is because the phone and PC markets are very different. Mobile operators are reluctant to allow third-software software on to their devices without certification, which is currently very costly and time-consuming. This discourages many software developers.”
But this is all set to change, if the project Massacci coordinates gains broad industry acceptance. “We have worked to reduce the threshold for certification without compromising security,” he says.
Certifiably safe
S3MS has developed a ‘security-by-contract’ technological solution which would allow users to download and use applications on a range of devices – from smart phones to personal digital assistants (PDAs) – without compromising their phone’s integrity or signing up to more than they bargained for. In contrast to the current e-signatures in place, users will be able to agree to, and even define, contracts that outline how and when an application is used.
“The current ‘sandbox’ security model is very simple: you either allow nothing or everything. With security-by-contract, you have more flexibility but also more complexity,” notes Massacci.
In practice, the new system will not prove that complex for end-users, developers and mobile operators. “Users will sign up to certain contractual agreements which specify such things as the number of SMSs an application can send, how many megabytes it can download, and even whether it can work when the power is low.”
Software developers will continue to develop code in the same way, except that they will have to “present an electronic contract and develop a verification process to the mobile operator”, according to Massacci.
This is a vast improvement on the current ‘trusted third-party’ certification which is complex and costly both for developers and operators, pushing it beyond the means of most companies.
“This means that operators will be able to formalise and streamline their third-party contracting process, generating a range of new business streams,” he elaborates.
Kaleidoscopic options
The beauty of the S3MS concept is that it is both flexible and scalable, which means that not all parties need to reach an accord for it to work. “In this model, we don’t assume that all partners – operators, developers and users – need to agree,” Massacci explains.
“The system allows operators to monitor for applications that violate its policies. It also allows the user to ‘inoculate’ applications that do not have a security policy. In addition, users and application providers can reach their own agreements without the operator.”
The EU-backed project insist that security-by-contract will not replace but enhance today’s security mechanism, and will provide a flexible, simple and scalable security and privacy protection for future mobile systems. The S3MS architecture provides an open platform for the development, loading and run-time execution of downloadable third-party applications on mobile platforms.
The project demonstrated a prototype of the system to some industry players in December 2007 and the final version of the prototype is due out in February 2008.
On the horizon
So, how likely are we to be using ‘security-by-contract’ in the future? Massacci is confident that it will be well received in the market. France telecom is a partner in S3MS and is finalising the commercial exploitation report. Japan’s DoCoMo is also a partner and Telecom Italia has expressed interest.
“We are in the process of trademarking ‘security-by-contract,” he says. “We will then discuss what to do after that and what kind of investments and investors we need to take the idea further.”
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
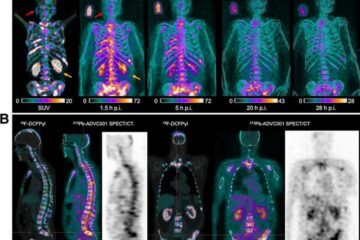
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















