Personal Touch Signature Makes Mobile Devices More Secure
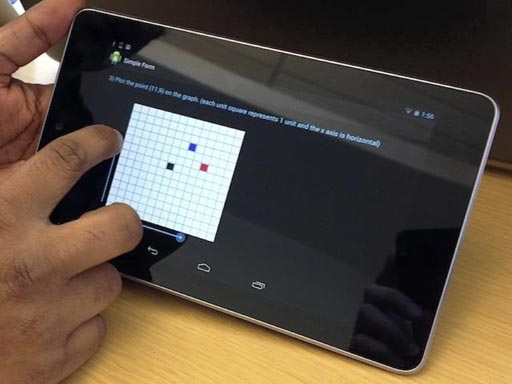
LatentGesture LatentGesture continuously monitors how a user taps and swipes a mobile device. If the movements don’t match the owner’s tendencies, the system recognizes the differences and can be programmed to lock the device.
Passwords, gestures and fingerprint scans are all helpful ways to keep a thief from unlocking and using a cell phone or tablet. Cybersecurity researchers from the Georgia Institute of Technology have gone a step further.
They’ve developed a new security system that continuously monitors how a user taps and swipes a mobile device. If the movements don’t match the owner’s tendencies, the system recognizes the differences and can be programmed to lock the device.
“The system learns a person’s ‘touch signature,’ then constantly compares it to how the current user is interacting with the device,” said Polo Chau, a Georgia Tech College of Computing assistant professor who led the study.
To test the system, Chau and his team set up an electronic form with a list of tasks for 20 participants. They were asked to tap buttons, check boxes and swipe slider bars on a phone and tablet to fill out the form. The system tracked their tendencies and created a profile for each person.
After profiles were stored, the researchers designated one person’s signature as the “owner” of the device and repeated the tests. LatentGesture successfully matched the owner and flagged everyone else as unauthorized users.
“Just like your fingerprint, everyone is unique when they use a touchscreen,” said Chau. “Some people slide the bar with one quick swipe. Others gradually move it across the screen. Everyone taps the screen with different pressures while checking boxes.”
The research team also programmed the system to store five touch signatures on the same device – one “owner” and four authorized users. When someone other than the owner used the tablet, the system identified each with 98 percent accuracy.
“This feature could be used when a child uses her dad’s tablet,” said College of Computing sophomore Premkumar Saravanan. “The system would recognize her touch signature and allow her to use the device. But if she tried to buy an app, the system could prevent it.”
The researchers say LatentGesture’s biggest advantage is that the system is constantly running in the background. The user doesn’t have to do anything different for added security and authentication.
“It’s pretty easy for someone to look over your shoulder while you’re unlocking your phone and see your password,” said Samuel Clarke, another College of Computing student on the research team. “This system ensures security even if someone takes your phone or tablet and starts using it.”
Chau is co-advising the project with Hongyuan Zha, a professor in the School of Computational Science and Engineering. The study will be presented in Toronto at ACM Chinese CHI 2014 from April 26 to 27.
This research was partially supported by the National Science Foundation (NSF) under grants IIS-1049694 and IIS-1116886. Any conclusions expressed are those of the principal investigator and may not necessarily represent the official views of the NSF.
Media Contact
More Information:
http://www.gatech.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Properties of new materials for microchips
… can now be measured well. Reseachers of Delft University of Technology demonstrated measuring performance properties of ultrathin silicon membranes. Making ever smaller and more powerful chips requires new ultrathin…

Floating solar’s potential
… to support sustainable development by addressing climate, water, and energy goals holistically. A new study published this week in Nature Energy raises the potential for floating solar photovoltaics (FPV)…
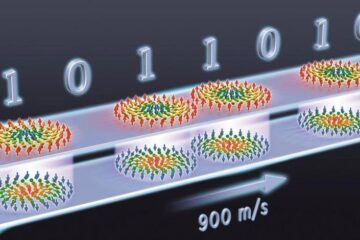
Skyrmions move at record speeds
… a step towards the computing of the future. An international research team led by scientists from the CNRS1 has discovered that the magnetic nanobubbles2 known as skyrmions can be…





















