Newly published cyber security report identifies key research priorities

Outcome of CSIT's Belfast 2011 Cyber Summit represents a global collective strategy for world's leading research institutes
Developing self-learning, self aware cyber security technologies, protecting smart utility grids and enhancing the security of mobile networks are among the top research priorities needed to safeguard the internet of tomorrow, according to a report released today.
Published by the UK's National Centre for Secure Information Technologies (CSIT), the report represents the outcome of discussions held during the inaugural World Cyber Security Technology Research Summit hosted by CSIT earlier this year.
The Belfast 2011 event attracted international cyber security experts from leading research institutes, government bodies and industry who gathered to discuss current cyber security threats, predict future threats and the necessary mitigation techniques, and to develop a collective strategy for next generation research.
The collective research strategy contained in the report identifies four research themes critical to the ongoing creation of cyber security defences:
Adaptive cyber security technologies – research objectives in this area will include the development of self-learning cyber security technologies; self-awareness in cyber systems; the establishment of feedback in cyber systems to learn from cyber attacks.
Protection of smart utility grids – research aims in this field will comprise: smart grid requirements gathering methodology; protection technologies for smart grid components; secure technologies for smart grid communications; smart grid and home area network integration that provides privacy and security of collected information; development of smart grid standards.
Security of the mobile platform and applications – research in this space will target not only malicious applications but also mobile cyber security problems introduced by the configuration and use of mobile networks, including network availability, mobile web browsers and caller authentication.
Multi-faceted approach to cyber security research – research will take into account social behavioural norms and societal desires in cyber space, cyber space policies, the impact of cyber and other legislation and the economics of cyber space and cyber security.
“Belfast 2011 brought together a diverse range of talent and knowledge in the cyber security field from which we have developed this strategy for next generation research,” says Prof John McCanny CSIT's Principal Investigator.
“Our ambition is that this strategy will help to inform global cyber security research and act as a driver for cyber security roadmap definition over the coming year. We will hold future summits at which changes in cyber security will be discussed and the proposed collective research strategies will be reviewed and developed.”
Notes to editors
Copies of the World Cyber Security Technology Research Summit Report – Belfast 2011 – are available from www.csit.qub.ac.uk
About Belfast 2011
Participants at the inaugural World Cyber Security Technology Research Summit included representatives of the UK Home Office, US Department of Commerce, US Cyber Consequences Unit, Stanford University, Carnegie Mellon University, BAE Systems, Thales and IBM.
About CSIT
The Centre for Secure Information Technologies (CSIT) is an innovation and knowledge centre based at Queen's University of Belfast's, Institute of Electronics, Communications and Information Technology (ECIT). Funded by EPSRC, TSB, Invest NI and industry collaborators, the Centre brings together research specialists in complementary fields such as data encryption, network security systems, wireless enabled security systems and intelligent surveillance technology.
CSIT is developing innovative and novel technology in both information and people security applications and is focused on key grand challenges (1) Secure Hyperconnected Networks (Smart Grid Security, Cloud Security, Cyber Security), (2) Secure Transport Corridors (Bus, Train, Airport Security) and (3) Security and Trust in the Financial Sector (e-Crime, Capital Market Security).
CSIT's member companies include: Altera, BAE Systems, Cisco, Q1Labs and Thales as well as government agencies with strong interests in this area. These include the Home Office, GCHQ, CESG, CPNI and DSTL.
Technologies being developed at CSIT include powerful computer processors that can detect and filter malware and cyber attacks within large networks in real-time, Physical Unclonable Functions that provide a lightweight and secure digital fingerprint for physical devices and an Intelligent Reasoning Algorithm that can take large volumes of multi-agent information from CCTV, RFID etc and rationalise and identify security events within transport networks.
For further information, please contact: Brian Arlow on +44 7860 289143
Media Contact
More Information:
http://www.csit.qub.ac.ukAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
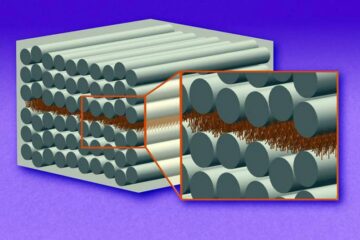
“Nanostitches” enable lighter and tougher composite materials
In research that may lead to next-generation airplanes and spacecraft, MIT engineers used carbon nanotubes to prevent cracking in multilayered composites. To save on fuel and reduce aircraft emissions, engineers…

Trash to treasure
Researchers turn metal waste into catalyst for hydrogen. Scientists have found a way to transform metal waste into a highly efficient catalyst to make hydrogen from water, a discovery that…
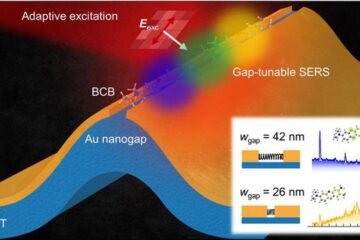
Real-time detection of infectious disease viruses
… by searching for molecular fingerprinting. A research team consisting of Professor Kyoung-Duck Park and Taeyoung Moon and Huitae Joo, PhD candidates, from the Department of Physics at Pohang University…





















