Keeping Secrets in a World of Spies and Mistrust

Even today’s encrypted data is vulnerable to technological progress. What privacy is ultimately possible? In the 27 March issue of Nature, the weekly international journal of science, researchers Artur Ekert and Renato Renner review what physics tells us about keeping our secrets secret.
In the history of secret communication, the most brilliant efforts of code-makers have been matched time and again by the ingenuity of code-breakers. Sometimes we can even see it coming. We already know that one of today’s most widely used encryption systems, RSA, will become insecure once a quantum computer is built.
But that story need not go on forever. “Recent developments in quantum cryptography show that privacy is possible under stunningly weak assumptions about the freedom of action we have and the trustworthiness of the devices we use,” says Ekert, Professor of Quantum Physics at the University of Oxford, UK, and Director of the Centre for Quantum Technologies at the National University of Singapore. He is also the Lee Kong Chian Centennial Professor at the National University of Singapore.
Over 20 years ago, Ekert and others independently proposed a way to use the quantum properties of particles of light to share a secret key for secure communication. The key is a random sequence of 1s and 0s, derived by making random choices about how to measure the particles (and some other steps), that is used to encrypt the message. In the Nature Perspective, he and Renner describe how quantum cryptography has since progressed to commercial prospect and into new theoretical territory.
Even though privacy is about randomness and trust, the most surprising recent finding is that we can communicate secretly even if we have very little trust in our cryptographic devices – imagine that you buy them from your enemy – and in our own abilities to make free choices – imagine that your enemy is also manipulating you. Given access to certain types of correlations, be they of quantum origin or otherwise, and having a little bit of free will, we can protect ourselves. What’s more, we can even protect ourselves against adversaries with superior technology that is unknown to us.
“As long as some of our choices are not completely predictable and therefore beyond the powers that be, we can keep our secrets secret,” says Renner, Professor of Theoretical Physics at ETH Zurich, Switzerland. This arises from a mathematical discovery by Renner and his collaborator about 'randomness amplification': they found that a quantum trick can turn some types of slightly-random numbers into completely random numbers. Applied in cryptography, such methods can reinstate our abilities to make perfectly random choices and guarantee security even if we are partially manipulated.
“As well as there being exciting scientific developments in the past few years, the topic of cryptography has very much come out of the shadows. It’s not just spooks talking about this stuff now,” says Ekert, who has worked with and advised several companies and government agencies.
The semi-popular essay cites 68 works, from the writings of Edgar Allen Poe on cryptography in 1841, through the founding papers of quantum cryptography in 1984 and 1991, right up to a slew of results from 2013.
The authors conclude that “The days we stop worrying about untrustworthy or incompetent providers of cryptographic services may not be that far away”.
Carolyn FONG
Senior Manager (Media Relations)
Office of Corporate Relations
National University of Singapore
DID: +65 6516 5399
Email: carolyn@nus.edu.sg
Media Contact
More Information:
http://www.nus.edu.sgAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Superradiant atoms could push the boundaries of how precisely time can be measured
Superradiant atoms can help us measure time more precisely than ever. In a new study, researchers from the University of Copenhagen present a new method for measuring the time interval,…
Ion thermoelectric conversion devices for near room temperature
The electrode sheet of the thermoelectric device consists of ionic hydrogel, which is sandwiched between the electrodes to form, and the Prussian blue on the electrode undergoes a redox reaction…
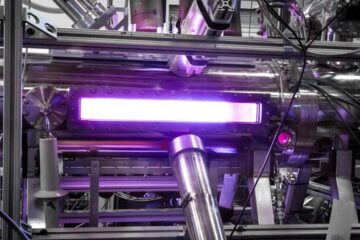
Zap Energy achieves 37-million-degree temperatures in a compact device
New publication reports record electron temperatures for a small-scale, sheared-flow-stabilized Z-pinch fusion device. In the nine decades since humans first produced fusion reactions, only a few fusion technologies have demonstrated…





















