Intelligent programs protect your computer environment

Intrusion detection systems (IDS) are security tools designed to monitor computer systems for suspicious events. To reduce the risk of intrusion, which is one of the threats to computer security, a team of researchers at UC3M have unveiled a multi-agent system that identifies suspicious events and autonomously determines whether or not any action should be taken. According to Professor Agustin Orfila of the Department of Informatics of the UC3M, both these are desirable features in an IDS.
At present, Spain lags behind in advancing investigations in multi-agent architectures for IDS compared to other countries. According to the investigator, the innovation behind the study is the use of deliberative agents that can adapt to the surroundings they are confronted with, and consider their past success in an independent manner to decide whether or not they should respond when facing a suspect event. This is achieved by using a “quantitative model that weighs the loss that an intrusion would provoke against the cost of taking responsive action”, Professor Orfila indicates. In this way, the IDS multi-agent determines the best system configuration for each scenario and decides if a response is appropriate, quantifying to what extent IDS supports the calculated decision. One of the most common intrusions attacks are the “port scan attack” (searching for open ports), denial-of-service attack, achieving unrestricted access to the target computer and triying to acces a computer remotely.
Farewell to intrusions
According to the National Institute of Standards and Technologies of the United States, “Intrusion detection is the process of detecting unauthorized use of, or attack upon, a computer or network. IDSs are software or hardware systems that detect such misuse.” Professor Orfila adds that an agent should be imparted with capabilities such as reactivity, sociability, self-initiative, adaptation, mobility, with a final result of representing a person. “In this way, the IDS multi-agent architecture allows us to distribute the detection load and better co-ordinate the process, with the consequence of accomplishing a more efficient detection”, explains the professor.
Security administrators would be the ideal users for the system because “it would allow them to quantify the value that the IDS attaches to its decisions and moreover, it would indicate how to adequately tune the IDS to its environment”, states Professor Orfila. Nevertheless, in order to implement its use, he adds, the IDS would have to be adapted to the traffic of the real network, the system would require to be trained for the concrete surroundings and the functionality would have to be evaluated in this real environment.
This study, published in the magazine Computer Communication under the title “Autonomous decision on intrusion detection with trained BDI agents”, has been developed by Agustín Orfila, Javier Carbó and Arturo Ribagorda, of the Grupo de Seguridad de las Tecnologías de la Información y las Comunicaciones and the Grupo de Inteligencia Artificial Aplicada of the Departamento de Informática of the UC3M.
Media Contact
More Information:
http://www.uc3m.esAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Properties of new materials for microchips
… can now be measured well. Reseachers of Delft University of Technology demonstrated measuring performance properties of ultrathin silicon membranes. Making ever smaller and more powerful chips requires new ultrathin…

Floating solar’s potential
… to support sustainable development by addressing climate, water, and energy goals holistically. A new study published this week in Nature Energy raises the potential for floating solar photovoltaics (FPV)…
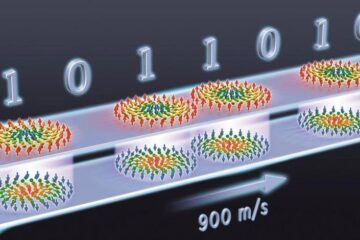
Skyrmions move at record speeds
… a step towards the computing of the future. An international research team led by scientists from the CNRS1 has discovered that the magnetic nanobubbles2 known as skyrmions can be…





















