Injecting Malicious Code Into HTML5-Based Apps

Can you imagine that simply doing these things can get your smarphones infected with “worms” that can not only steal personal information from your phone, but also infect your friends's phones.
Sound scary? It will not be long before worms like this spread among smartphones. What makes the attacks feasible is an emerging technology called HTML5-based app development, and it has been rapidly gaining popularity in the mobile industry.
When the adoption of this technology reaches certain threshold, attacks like this will become quite common, unless we do something to stop it. A recent Gartner report says that by 2016, fifty percent of the mobile apps will be using HTML5-based technologies.
What platforms are affected?
All major mobile systems will be affected, including Android, iOS, Blackberry, Windows Phone, etc., because they all support HTML5-based mobile apps.
A notorious problem of the HTML5-based technology is that malicious code can be easily injected into the program and get executed. That is why the Cross-Site Scripting (XSS) attack is still one of the most common attacks in the Web.
XSS attacks can only target at web applications through a single channel (i.e. the Internet), but with the adoption of the same technology in mobile devices, we have found out that a similar type of attack can not only be launched against mobile apps, it can attack from many channels, including 2D barcode, Wi-Fi scanning, Bluetooth pairing, MP3 songs, MP4 videos, SMS messages, NFC tags, Contact list, etc. As long as an HTML5-based app displays information obtained from outside or from anohter app, it may be a potential victim.
Media Contact
More Information:
http://www.cis.syr.edu/~wedu/attack/All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Combatting disruptive ‘noise’ in quantum communication
In a significant milestone for quantum communication technology, an experiment has demonstrated how networks can be leveraged to combat disruptive ‘noise’ in quantum communications. The international effort led by researchers…
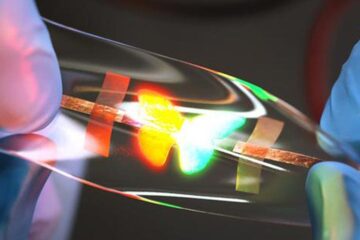
Stretchable quantum dot display
Intrinsically stretchable quantum dot-based light-emitting diodes achieved record-breaking performance. A team of South Korean scientists led by Professor KIM Dae-Hyeong of the Center for Nanoparticle Research within the Institute for…

Internet can achieve quantum speed with light saved as sound
Researchers at the University of Copenhagen’s Niels Bohr Institute have developed a new way to create quantum memory: A small drum can store data sent with light in its sonic…





















