Off the Hook! Who Gets Phished and Why

Communication researchers at four major universities have found that if you receive a lot of email, habitually respond to a good portion of it, maintain a lot of online relationships and conduct a large number of transactions online, you are more susceptible to email phishing expeditions than those who limit their online activity.
The study, “Why Do People Get Phished?” forthcoming in the journal, “Decision Support Systems and Electronic Commerce,” uses an integrated information processing model to test individual differences in vulnerability to phishing.
The study is particularly pertinent, given the rash of phishing expeditions that have become public of late, the most recent involving the online marketing firm Epsilon, whose database was breached last week by hackers, potentially affecting millions of banking and retail customers.
The authors are Arun “Vish” Vishwanath, PhD, associate professor in the UB Department of Communication, College of Arts and Sciences, and an expert in consumer behavior, specifically the diffusion and acceptance of information technology; H. Raghav Rao, PhD, SUNY Distinguished Service Professor in the UB Department of Management Science and Systems, School of Management, who conducts research on decision support systems, e-business, emergency response management systems and information assurance; Tejaswini Herath, PhD, Brock University (Ont., CA); Rui Chen, PhD, Ball State University, and Jingguo Wang, PhD, University of Texas, Arlington. Herath, Chen and Wang all earned degrees from UB.
Email “phishing” is a process that employs such techniques as using the names of credible businesses (American Express, eBay), government institutions (Internal Revenue Service, Department of Motor Vehicles), or current events (political donations, Beijing Olympic tickets, aiding Katrina victims) in conjunction with statements invoking fear, threat, excitement, or urgency, to persuade people to respond with personal and sensitive information like usernames, passwords and credit card details.
Phishing exploits what are generally accepted to be the poor current web security technologies, but Vishwanath says, “By way of prevention, we found that spam blockers are imperative to reduce the number of unnecessary emails individuals receive that could potentially clutter their information processing and judgment.
“At the other end,” he says, “individuals need to be extra careful when utilizing a single email account to respond to all their emails. An effective strategy is to use different email accounts for different purposes. If one email address is used solely for banking and another is used solely for personal communication with family and friends, it will increase your attention to the details of the email and reduce the likelihood of chance deception because of clutter.”
Vishwanath also advocates setting aside time to focus and respond to personal emails separately from work-related emails. For instance, setting aside a time each day for responding to personal banking emails gives you time to process them more clearly and consider their legitimacy before responding.
The integrated information processing model of phishing susceptibility presented in this study is grounded in prior research in information processing and interpersonal deception.
“We refined and validated our model using a sample of intended victims of an actual phishing attack,” Vishwanath says.
Overall, their model explains close to fifty percent of the variance in individual phishing susceptibility.
“Our results indicate that people process most phishing emails peripherally and make decisions based on simple cues embedded in the email. Interestingly, urgency cues, i.e., threats and warnings, in the email stimulated increased information processing, short-circuiting the resources available for attending to other cues that could potentially help detect the deception.
“Our findings suggest that habitual patterns of media use combined with high levels of email load have a strong and significant influence on individuals' likelihood to be phished.”
The study also showed that a person's competency with computing did not protect them from phishing scams, but their awareness about phishing in conjunction with healthy email habits, helped them avoid online deception.
Herath, who holds a PhD from UB, is an assistant professor in the Faculty of Business at Brock University. Chen, who holds a bachelor's and master's degree in computer science and a PhD in management science and systems from UB, is an assistant professor of information systems at Ball State. Wang, who holds a master's degree in industrial engineering and a PhD in management science and systems from UB, is an assistant professor of information systems and operations management, University of Texas, Arlington.
The University at Buffalo is a premier research-intensive public university, a flagship institution in the State University of New York system and its largest and most comprehensive campus. UB's more than 28,000 students pursue their academic interests through more than 300 undergraduate, graduate and professional degree programs. Founded in 1846, the University at Buffalo is a member of the Association of American Universities.
Media Contact
More Information:
http://www.buffalo.eduAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
High-energy-density aqueous battery based on halogen multi-electron transfer
Traditional non-aqueous lithium-ion batteries have a high energy density, but their safety is compromised due to the flammable organic electrolytes they utilize. Aqueous batteries use water as the solvent for…

First-ever combined heart pump and pig kidney transplant
…gives new hope to patient with terminal illness. Surgeons at NYU Langone Health performed the first-ever combined mechanical heart pump and gene-edited pig kidney transplant surgery in a 54-year-old woman…
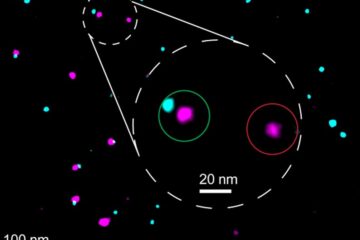
Biophysics: Testing how well biomarkers work
LMU researchers have developed a method to determine how reliably target proteins can be labeled using super-resolution fluorescence microscopy. Modern microscopy techniques make it possible to examine the inner workings…





















