Genetics Inspired Research Prevents Cyber Attacks

Now Wake Forest University researchers are fighting the continual evolution of viruses, worms and malware with evolution by developing the first-ever automated computer configurations that adjust as quickly as the threats.
Computer Science Associate Professor Errin Fulp and graduate student Michael Crouse are refining a genetically inspired algorithm that proactively discovers more secure computer configurations by leveraging the concept of “survival of the fittest.” Early simulations have shown the increased diversity of each device’s configuration improves overall network safety, without putting undue stress on IT administrators.
“Typically, administrators configure hundreds and sometimes thousands of machines the same way, meaning a virus that infects one could affect any computer on the same network,” says Crouse, who recently was named one of the “nation’s top new inventors” by Inventor’s Digest magazine. “If successful, automating the ability to ward off attacks could play a crucial role in protecting highly sensitive data within large organizations.”
Funded by a grant from Pacific Northwest National Laboratory (PNNL), the researchers aim to improve defense mechanisms of similar computing infrastructures with minimal human interaction.
Cyber attacks usually take place in two phases, says Fulp. In the reconnaissance phase, a virus simply observes the landscape, identifies possible defense mechanisms and looks for the best way in. If nothing has changed since the reconnaissance phase upon return, the virus strikes. But security experts say even the slightest change in environment can make a huge difference in deterring potential attackers.
“If we can automatically change the landscape by adding the technological equivalent of security cameras or additional lighting, the resulting uncertainty will lower the risk of attack,” explains Fulp.
Researchers are currently testing their work to transform cyber security. Planned assessment includes integrating the automated system into the computer science department’s annual “hackathon,” giving budding developers the opportunity to improve the system.
Though no one has successfully modeled this complex process before, this is not the first time Fulp and Crouse have turned to nature to guide their research. Read more about their bio-inspired projects to improve cyber security at http://go.wfu.edu/bioinspiration.
Media Contact
All latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles
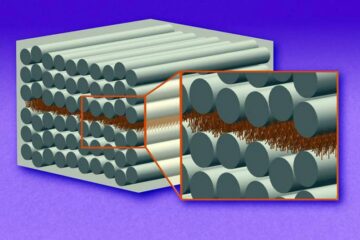
“Nanostitches” enable lighter and tougher composite materials
In research that may lead to next-generation airplanes and spacecraft, MIT engineers used carbon nanotubes to prevent cracking in multilayered composites. To save on fuel and reduce aircraft emissions, engineers…

Trash to treasure
Researchers turn metal waste into catalyst for hydrogen. Scientists have found a way to transform metal waste into a highly efficient catalyst to make hydrogen from water, a discovery that…
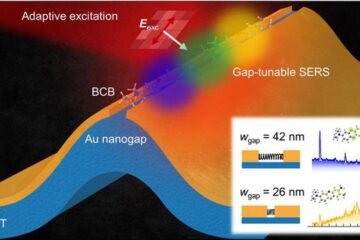
Real-time detection of infectious disease viruses
… by searching for molecular fingerprinting. A research team consisting of Professor Kyoung-Duck Park and Taeyoung Moon and Huitae Joo, PhD candidates, from the Department of Physics at Pohang University…





















