Build safety into the very beginning of the computer system

Commonly known as the Basic Input/Output System (BIOS), this fundamental system firmware—computer code built into hardware—initializes the hardware when you switch on the computer before starting the operating system. BIOS security is a new area of focus for NIST computer security scientists.
“By building security into the firmware, you establish the foundation for a secure system,” said Andrew Regenscheid, one of the authors of BIOS Protection Guidelines (NIST Special Publication 800-147). Without appropriate protections, attackers could disable systems or hide malicious software by modifying the BIOS. This guide is focused on reducing the risk of unauthorized changes to the BIOS.
Designed to assist computer manufacturers writing BIOS code, SP 800-147 provides guidelines for building features into the BIOS that help protect it from being modified or corrupted by attackers. Manufacturers routinely update system firmware to fix bugs, patch vulnerabilities and support new hardware. SP 800-147 calls for using cryptographic “digital signatures” to authenticate the BIOS updates before installation based on NIST's current cryptographic guidelines.* The publication is available just as computer manufacturers are beginning to deploy a new generation of BIOS firmware. “We believe computer manufacturers are ready to implement these guidelines and we hope to see them in products soon,” said Regenscheid.
The publication also suggests management best practices that are tightly coupled with the security guidelines for manufacturers. These practices will help computer administrators take advantage of the BIOS protection features as they become available.
BIOS Protection Guidelines, NIST SP 800-147, is available at http://csrc.nist.gov/publications/nistpubs/800-147/NIST-SP800-147-April2011.pdf.
* See Digital Signature Standard (FIPS 186-3, June 2009) at http://csrc.nist.gov/publications/fips/fips186-3/fips_186-3.pdf,
Recommendation for Key Management – Part 1: General (NIST SP 800-57, March 2008) at http://csrc.nist.gov/publications/nistpubs/800-57/sp800-57-Part1-revised2_Mar08-2007.pdf, and
Recommendation for Obtaining Assurances for Digital Signature Applications (NIST SP 800-89, November 2006) at http://csrc.nist.gov/publications/nistpubs/800-89/SP-800-89_November2006.pdf
Media Contact
More Information:
http://www.nist.govAll latest news from the category: Information Technology
Here you can find a summary of innovations in the fields of information and data processing and up-to-date developments on IT equipment and hardware.
This area covers topics such as IT services, IT architectures, IT management and telecommunications.
Newest articles

Bringing bio-inspired robots to life
Nebraska researcher Eric Markvicka gets NSF CAREER Award to pursue manufacture of novel materials for soft robotics and stretchable electronics. Engineers are increasingly eager to develop robots that mimic the…

Bella moths use poison to attract mates
Scientists are closer to finding out how. Pyrrolizidine alkaloids are as bitter and toxic as they are hard to pronounce. They’re produced by several different types of plants and are…
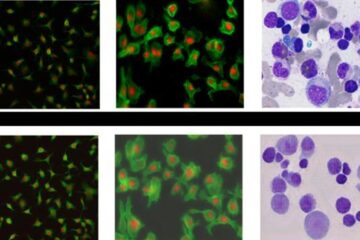
AI tool creates ‘synthetic’ images of cells
…for enhanced microscopy analysis. Observing individual cells through microscopes can reveal a range of important cell biological phenomena that frequently play a role in human diseases, but the process of…





















