SecureCloud 2012 in Frankfurt

How will changes in European data protection regulation affect cloud providers and users? How will forensics look like in the Cloud? These are some of the topics discussed by 250 experts from science, industry and politics at the SecureCloud Conference 2012 from May 9-10, 2012 in Frankfurt. SecureCloud 2012 is the premier European educational and networking event on cloud computing security and privacy.
This year, the agenda is set to arm participants with information, guidance and recommendations on the most important issues in cloud security including mobile, legal and policy. The event is co-hosted and organized by the Cloud Security Alliance (CSA), the European Network and Information Security Agency (ENISA), the Center for Advanced Security Research (CASED), the Fraunhofer Institute for Secure Information technology and the worldwide association of IS professionals ISACA.
The event will host a series of keynote presentations given by the foremost authorities and thought leaders in cloud security, including Robert Bohn, Reference Architecture Lead for the NIST Cloud Computing Program of Applied and Computational Sciences Division of NIST/ITL; Dr. Carl-Christian Buhr, European Commission and Cabinet Member for Vice-President Neelie Kroes; Billy Hawkes, Irish Data Protection Commissioner and Eran Feigenbaum Director of Security, Google Apps at Google. The format will allow for the opportunity for political and corporate decision-makers to learn first-hand how some of the most well-known and respected companies in the world are addressing cloud security through interactive sessions and networking events.
Dr. Carl-Christian Buhr, European Commission Cabinet Member of Vice-President Neelie Kroes, during his keynote, said he was pleased to hear that the CSA will be launching its certification framework, also announced today. The European Commission (EC) will include in the European Cloud Strategy document, which will be published this summer, an action on certification. The EC doesn't foresee any European mandatory certification scheme, but encourages and supports a market-driven, bottoms-up approach for security certification for cloud computing services and providers.
“Privacy and data protection are fundamental rights to the European citizens,” said Billy Hawkes, Irish Data Protection Commissioner. “Therefore, as a customer I should not have to worry about how companies process and store my data. On the other hand, small companies face a big challenge if they want to offer full transparency and accountability to their customers. Within the new EU data protection regulations we have to find ways to support companies, e. g., with certification systems for cloud providers they can rely on.”
“Cloud Computing already is a part of our daily life and work. But to securely unlock the full potential of this technology, scientists, cloud providers and users have to act in concert,” said Prof. Ahmad-Reza Sadeghi, Scientific Director at Fraunhofer SIT. “IT Security has become important for all new technologies. For Cloud Computing however, it is a precondition. The smallest technical inconsistencies or negligence can cause dramatic consequences. Companies need standardized guidelines and innovative solutions, therefore we have to further increase research and development in this area.“
“The European Commission has set out an ambitious digital agenda in its policy for cloud computing,” said Daniele Catteddu, Managing Director, EMEA for the CSA. “However, cloud computing needs to be more sufficiently addressed across the European legal frameworks and much further research needs to be done to address the challenges of European law on competition, network regulation and electronic commerce for clouds to operate in this market. It is our intention to bring these issues to light and provide a forum for collaboration and guidance to our participants.”
The conference program will also include a focus on mobile cloud computing. With mobile computing experiencing tremendous growth and adoption, mobile devices are gaining significant power and dynamic capabilities. Personally owned and potentially insecure mobile devices are increasingly being used to access employers’ systems and cloud-hosted data. Conference speakers will provide information and research to help participants understand the critical need to secure mobile endpoints from a cloud-centric vantage point.
About the Cloud Security Alliance
The Cloud Security Alliance is a not-for-profit organization with a mission to promote the use of best practices for providing security assurance within Cloud Computing, and to provide education on the uses of Cloud Computing to help secure all other forms of computing. The Cloud Security Alliance is led by a broad coalition of industry practitioners, corporations, associations and other key stakeholders. For further information, visit us at www.cloudsecurityalliance.org, and follow us on Twitter @cloudsa.
About CASED and Fraunhofer SIT
The Fraunhofer Institute for Secure Information Technology is Germany’s leading expert for applied research in IT Security. Its over 160 employees develop solutions for immediate use, tailored to the customer's needs. Together with its partner universities the Institute teams up in the Center for Advanced Security Research Darmstadt (CASED), Germany´s largest research center for IT Security.
About ISACA
With 95,000 constituents in 160 countries, ISACA (www.isaca.org) is a leading global provider of knowledge, certifications, community, advocacy and education on information systems (IS) assurance and security, enterprise governance and management of IT, and IT-related risk and compliance. Founded in 1969, the nonprofit, independent ISACA develops international IS auditing and control standards that help its constituents ensure trust in, and value from, information systems. It also advances and attests IT skills and knowledge through the globally respected Certified Information Systems Auditor (CISA), Certified Information Security Manager (CISM), Certified in the Governance of Enterprise IT (CGEIT) and Certified in Risk and Information Systems Control (CRISC) designations. ISACA continually updates COBIT, which helps IT professionals and enterprise leaders fulfill their IT governance and management responsibilities. Follow ISACA on Twitter at https://twitter.com/ISACANews.
About ENISA
The European Network and Information Security Agency (ENISA) is a centre of network and information security expertise for the EU, its member states, the private sector and Europe’s citizens. ENISA works with these groups to develop advice and recommendations on good practice in information security. It assists EU member states in implementing relevant EU legislation and works to improve the resilience of Europe’s critical information infrastructure and networks. ENISA seeks to enhance existing expertise in EU member states by supporting the development of cross-border communities committed to improving network and information security throughout the EU. More information about ENISA and its work can be found at www.enisa.europa.eu.
Media Contact
More Information:
http://www.sit.fraunhofer.de/All latest news from the category: Event News
Newest articles
Silicon Carbide Innovation Alliance to drive industrial-scale semiconductor work
Known for its ability to withstand extreme environments and high voltages, silicon carbide (SiC) is a semiconducting material made up of silicon and carbon atoms arranged into crystals that is…
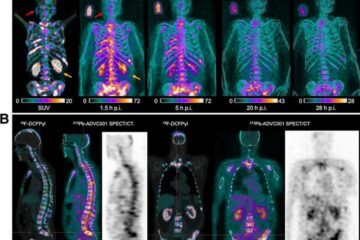
New SPECT/CT technique shows impressive biomarker identification
…offers increased access for prostate cancer patients. A novel SPECT/CT acquisition method can accurately detect radiopharmaceutical biodistribution in a convenient manner for prostate cancer patients, opening the door for more…

How 3D printers can give robots a soft touch
Soft skin coverings and touch sensors have emerged as a promising feature for robots that are both safer and more intuitive for human interaction, but they are expensive and difficult…





















